Audit-Ready Identity &
Access Governance
GOVERNANCE PLATFORM FOR THE AI ERA
Where Identity Governance, Application
Controls and Audit Converge
As identities scale, manual processes create risk and inefficiency. Automate core identity governance processes, including:
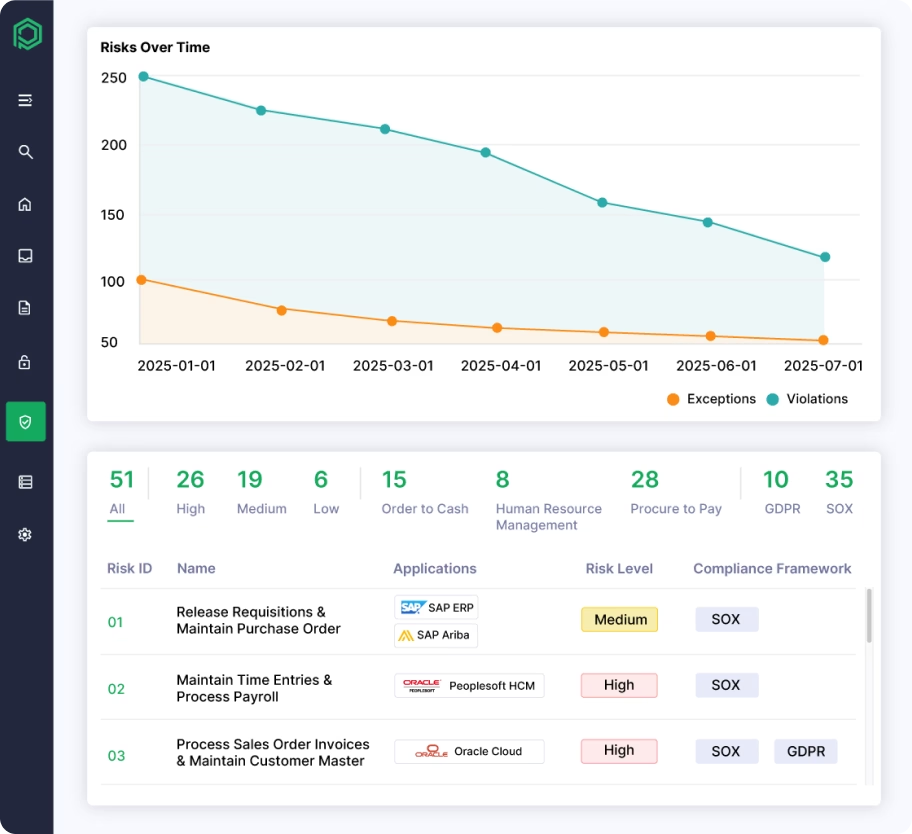
Compliant Provisioning
Automate employee onboarding and offboarding (Joiner/Mover/Leaver).
Access Requests
Self-service portal for users to easily request the apps they need.
Access Certifications
Automate manager access reviews to easily pass audits.
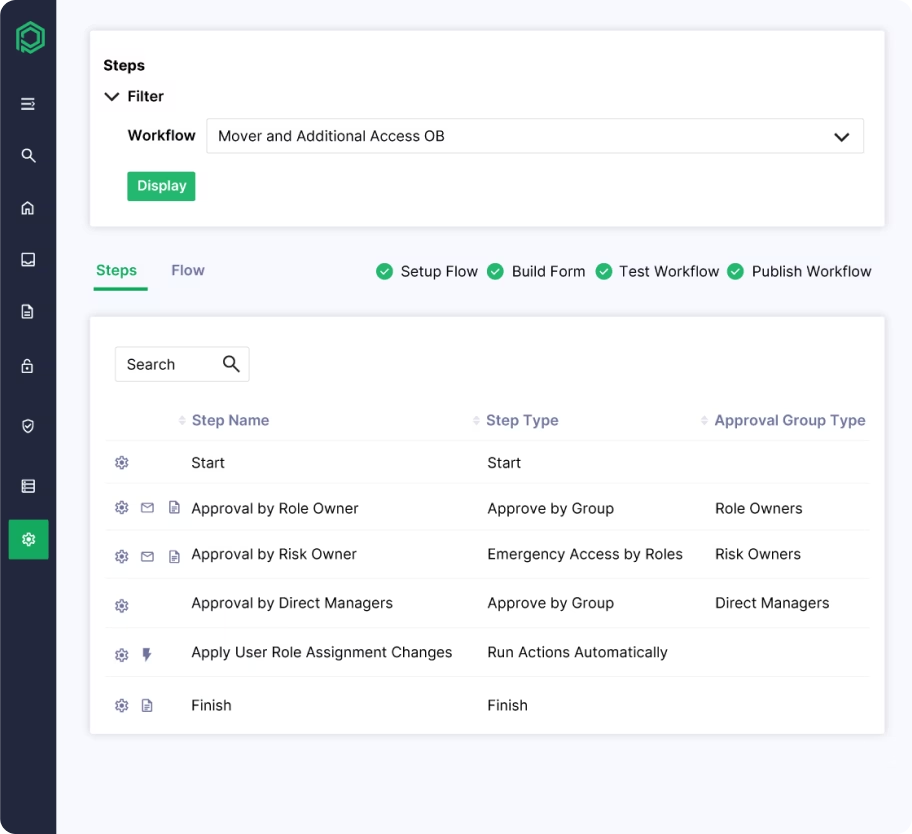
Role Management
Automatically group and assign permissions based on a user's job title.
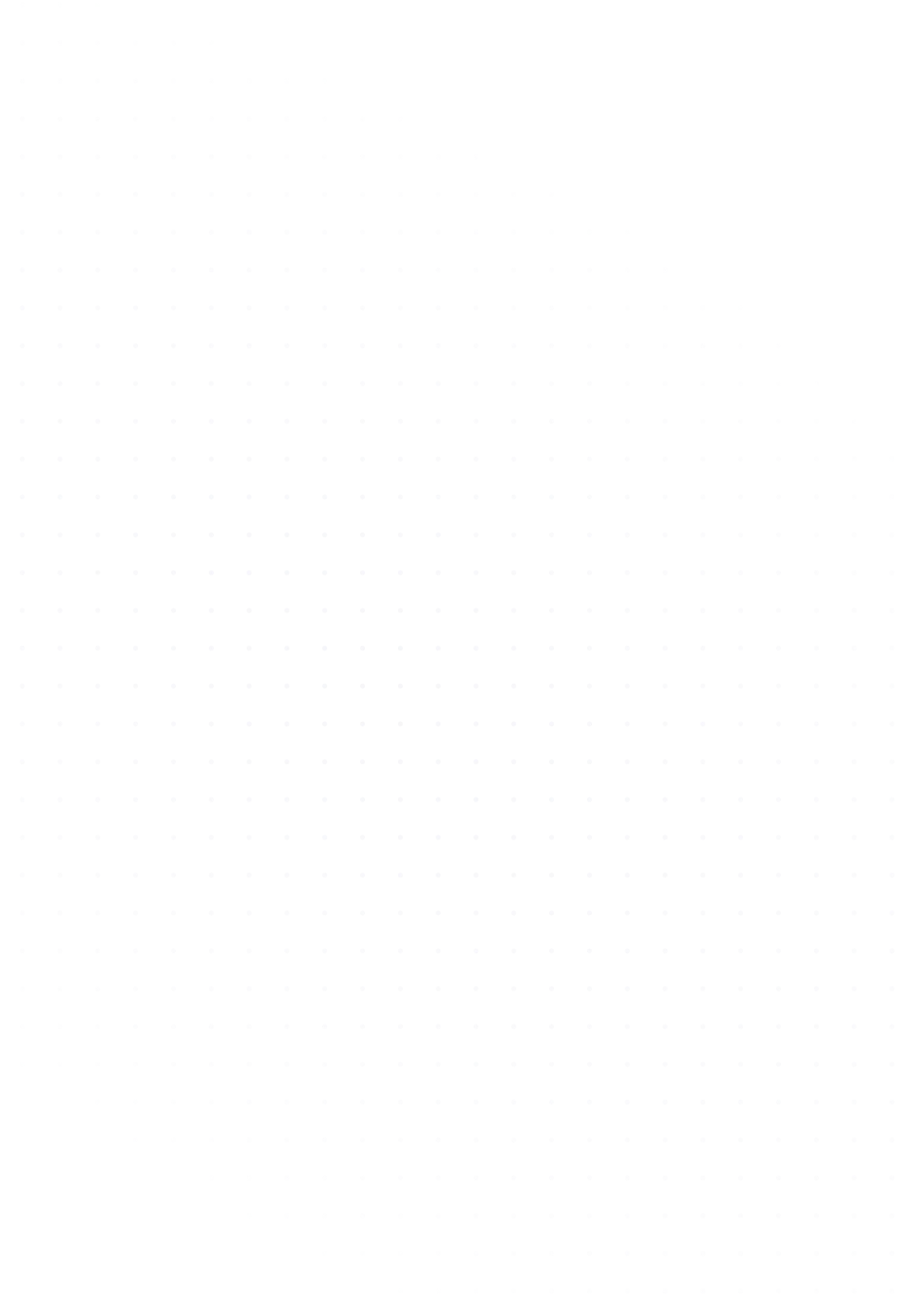
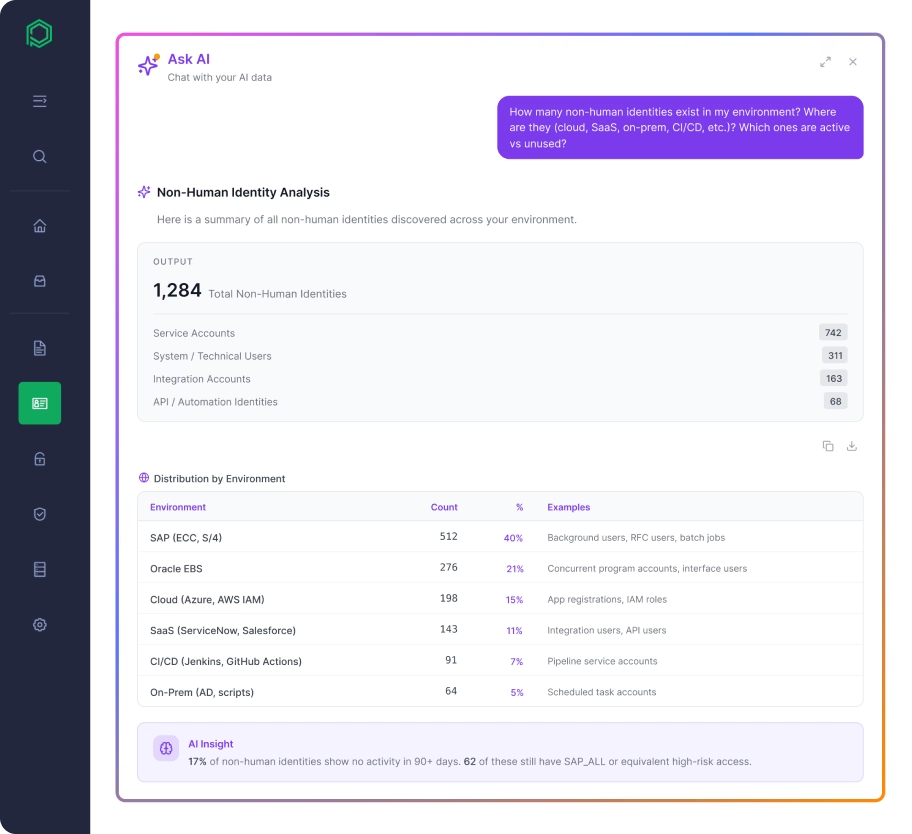
Governance gaps drive risk. Close them before they lead to fraud, control failures, or audit findings by automating:
Separation of Duties (SoD)
Identify and block toxic and high-risk access combinations.
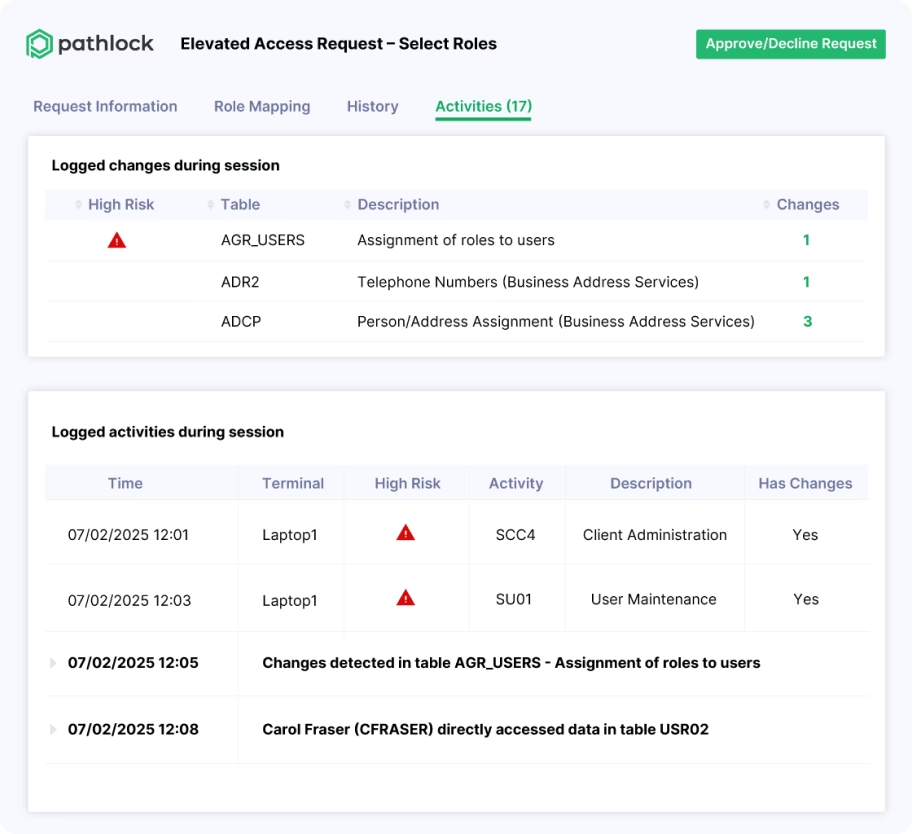
Emergency Access
Secure, fully tracked "break-glass" access for admins.
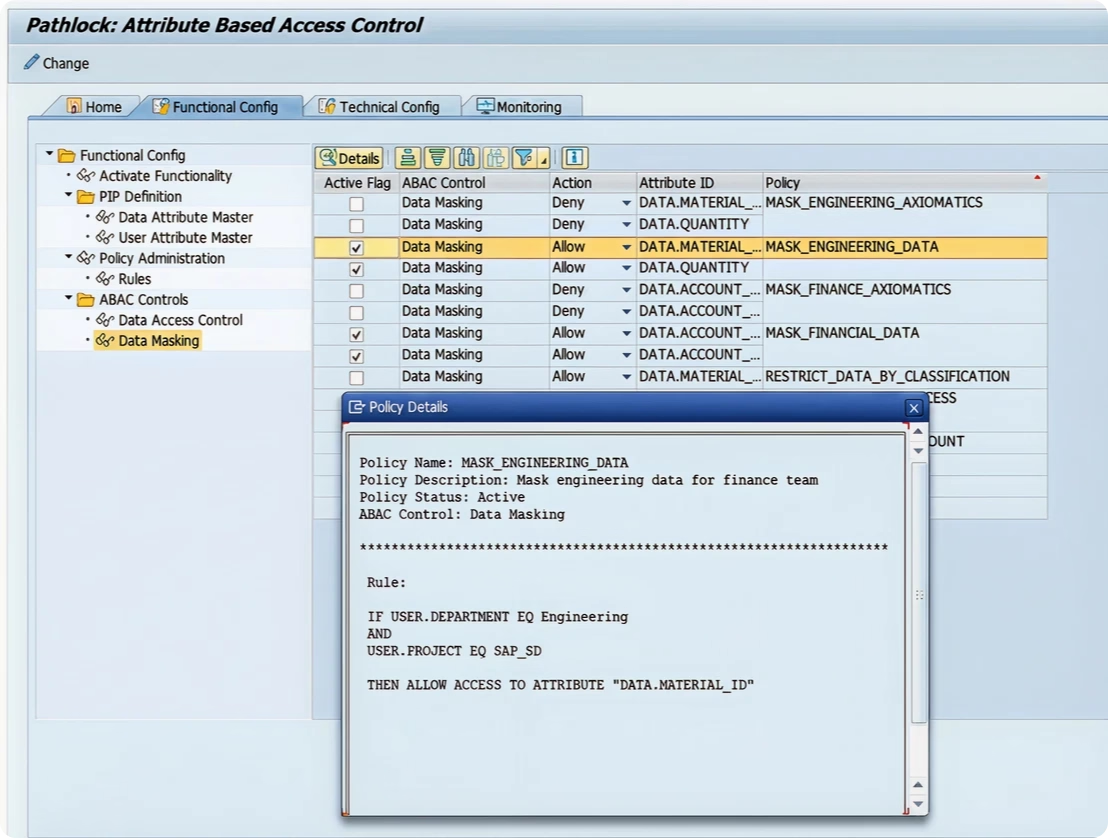
Dynamic Access Control
Conditionally mask data or block sensitive transactions in real time.
Entitlement Design
Build and test secure, compliant roles for your ERP applications.
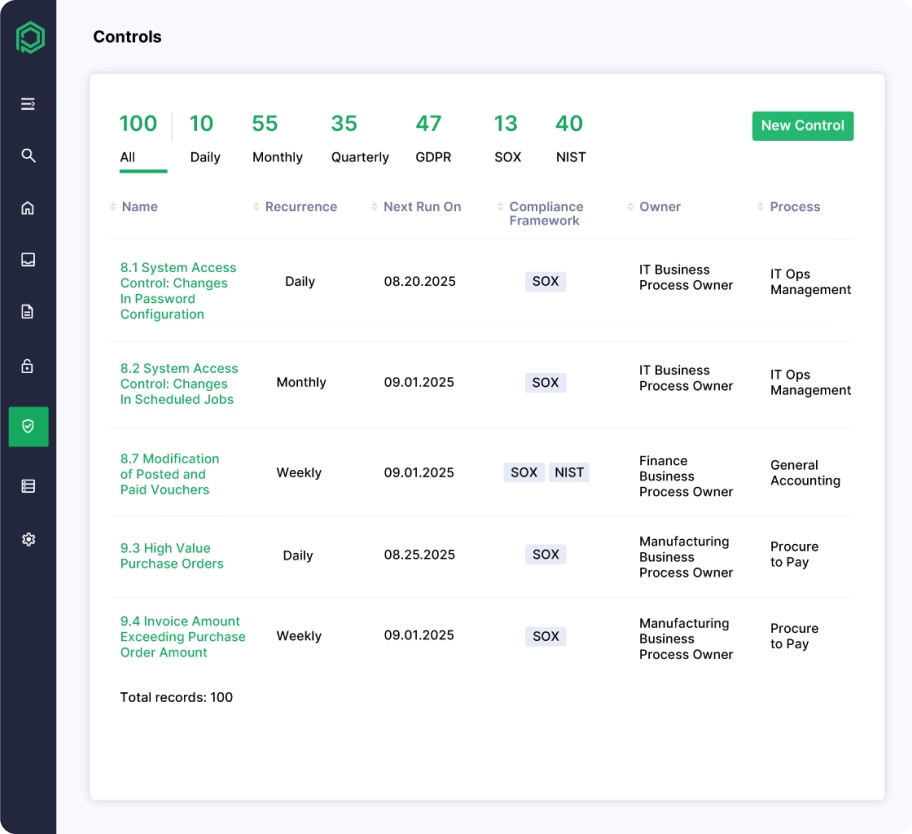
It’s one thing to implement controls—it’s another to prove they work. Pathlock automates audit and assurance processes, including:
Continuous Controls Monitoring
Real-time alerts the second a compliance rule or IT policy is broken.
Enriched Transaction Monitoring
Analyze financial transactions with added context to pinpoint actual fraud.
Audit Trails
A tamper-proof log showing exactly who changed what data, and when.
Audit Reporting
Out-of-the-box evidence and reports to hand straight to external auditors.
Unpatched vulnerabilities and active threats can bypass governance controls. Pathlock secures ERP systems by automating:
“Pathlock ensured compliant provisioning and identity lifecycle management”
“Pathlock automated our SoD analysis, streamlining compliance”
“Pathlock streamlined our SOX audits by helping us identify true SoD violations”
“With Pathlock, we can now investigate and respond to critical events much faster”
Pre-Built Connectors for 150+ Applications,
No-Code Tools for Custom Integrations
Identity & Access Governance Built for Today, Ready for What’s Next
We deliver the core capabilities required to meet today’s audit, compliance, and security demands — with the scalability and flexibility to support future growth and evolving risks.
The World’s Leading
Enterprises Trust Pathlock
Proven Leader in Identity Governance, Risk, and Compliance



Deployed in Partnership with the World’s Top Systems Integrators
“At KPMG, we are committed to innovation and collaboration, which is why we chose to collaborate with Pathlock — a leader redefining identity security…”
Expert Insights and Best Practices
Latest Pathlock News
Stay up to date with Pathlock's most recent announcements and thought leadership.