Pathlock for Business Application Owners
Automate the process of enforcing proper controls for the buiness apps your company relies upon every day.
Reduce Application Risk by Automating Access Controls
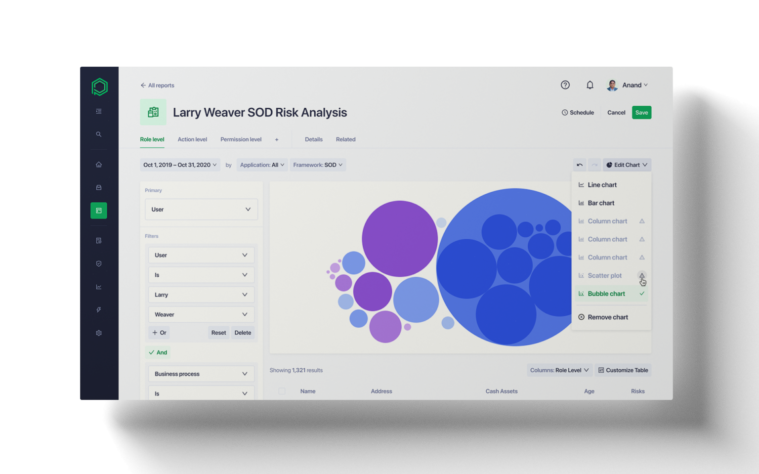
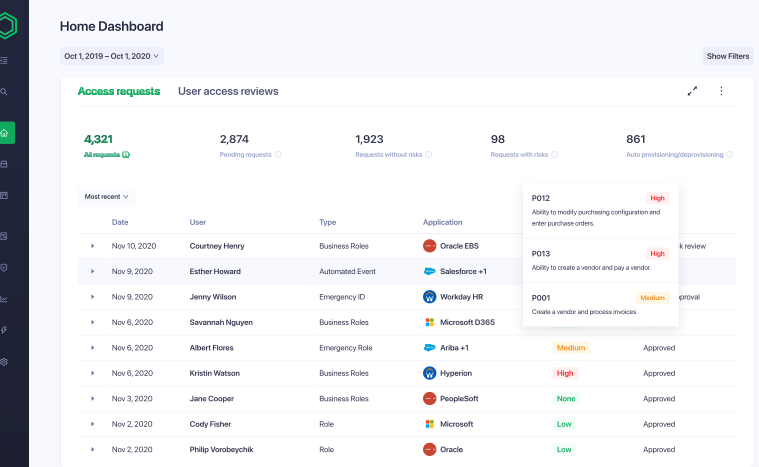
Pathlock allows application owners to automate the appropriate operational, management and technical controls that help mitigate and manage security and compliance risks facing enterprise applications, end users, and the business.
The Global 2000 standardizes on Pathlock to speed up audit processes, prioritize alerts for faster remediation, track individual transactions across the leading business applications out-of-the-box, detect malicious transactions (including potential instances of fraud and Segregation of Duties violations), uncover unauthorized changes to customer profiles or master data files, and comply with regulations and standards (i.e, SOX, HIPAA, GDPR, PCI/D).
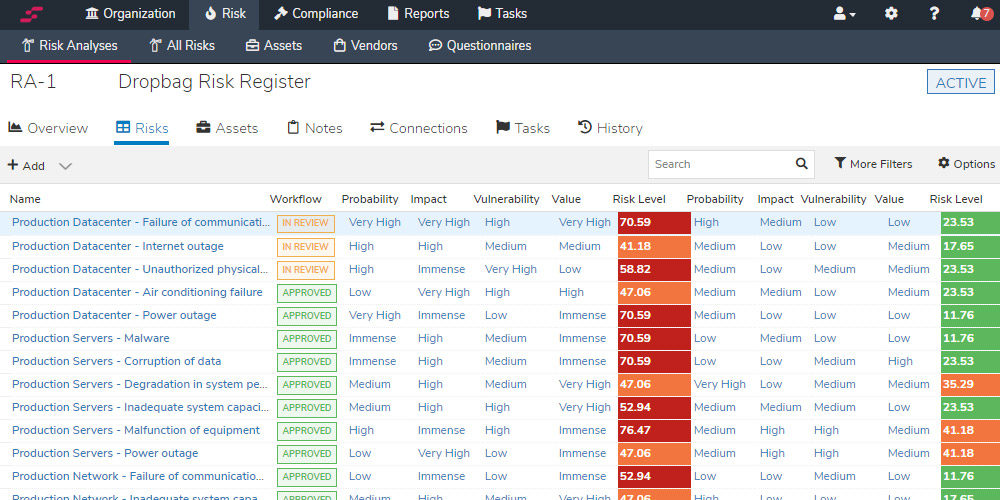
Continuosly Monitor For Application Configuration Changes And Reduce Risk of Downtime
Monitor changes to sensitive configurations across application environments, including cloud, on-premises and hybrid solutions. Be alerted to changes in real time, so you can prevent application down time and ensure business continuity.

![[Webinar] Microsoft Entra ID Governance: How to Create Efficient and Secure Access Management Across Your Entire Business Landscape](https://pathlock.com/wp-content/uploads/2025/06/Screenshot-2025-06-18-at-3.24.10 PM-294x178.png)
![[Webinar] Fix Oracle Risk and Compliance Gaps Before They Cost You — With One Platform](https://pathlock.com/wp-content/uploads/2025/06/videocovermain-294x178.png)
![[Webinar] What a Former FBI Agent Wants Every Healthcare Security Team to Know](https://pathlock.com/wp-content/uploads/2025/06/fbi-294x178.png)
![[Webinar] Zero Trust for Export Controlled Information in SAP](https://pathlock.com/wp-content/uploads/2025/05/Screenshot-2025-05-23-at-11.53.14 AM-294x178.png)
![[Webinar] From ‘Oh No’ to Go-Live: De-Risk Your SAP Role Migration](https://pathlock.com/wp-content/uploads/2025/05/videocoverroledesign-294x178.png)


![[Webinar] Governance on Autopilot:Automate Compliance & Take Control of ERP Security](https://pathlock.com/wp-content/uploads/2025/04/heroimage1-294x178.png)