Identity Governance, Risk and Compliance Solution for SAP ERP
AUDIT-PROOF. FUTURE-PROOF. ROI-DRIVEN.

tasks automated
access violations
over 3 years
Go Beyond Traditional
Identity Governance
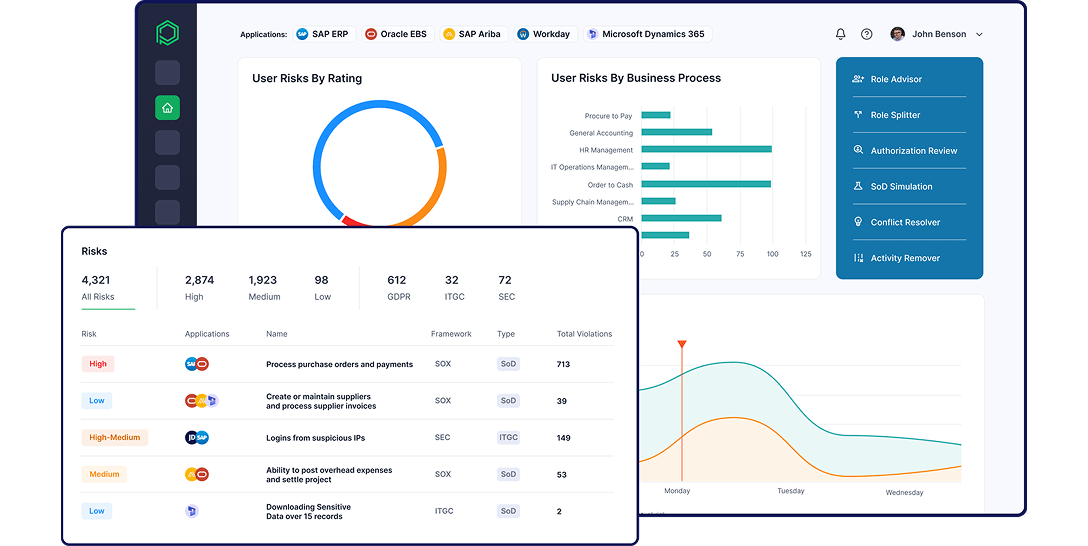
- Remediate SoD risks across SAP and connected applications
- Automate compliant user provisioning and de-provisioning
- Run efficient UAR campaigns to validate entitlements
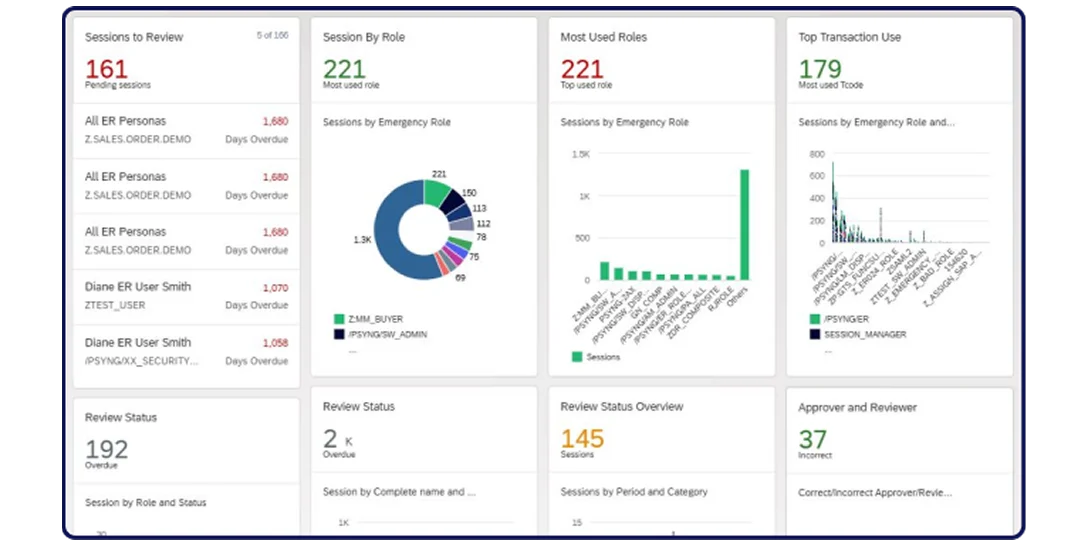
- Control Firefighter access with audit-ready logs and automated revocation
- Continuously optimize roles to simplify ongoing access governance
- Centralize and automate business and IT control monitoring across SAP
- Detect and alert on configuration changes, policy breaches, and anomalies
- Quantify risk impact from financial transactions to prioritize remediation
- Continuously scan SAP systems to detect vulnerabilities
- Monitor and respond to threats in real time
- Secure custom ABAP code with automated scanning
- Control transports across dev, QA, and production
- Understand the complete technical flow of customer transactions in custom applications
- Automates discovery and classification of sensitive data
- Apply real-time, attribute-based masking to sensitive SAP fields
- Protects sensitive production data in non-production environments with scrambling
- Grant or restrict access in real time with dynamic attribute-driven authorizations
- Continuously monitor SAP data access
Pathlock delivers Identity Governance, GRC and Cybersecurity that never touch your SAP Core

Providing an Unmatched Level of Insight and Efficiency
Pathlock Recognized as a Leader in SAP Access Control and Security
Key Initiatives
Discover how Pathlock can help you address your unique business challenges with SAP ERP and beyond.
Schedule One-to-One DemoDigital Transformation
Over 50% of ERP projects exceed budgets and timelines. Pathlock helps you streamline digital transformation and modernization success.
Learn More
SOX Compliance
40% of organizations fail at least one SOX control annually. Pathlock helps you prevent audit failures, restatements, and reputational damage.
Learn More
Audit Readiness
Companies spend 20,000+ hours yearly on compliance. Pathlock automates error-prone manual processes to streamline audit preparation.
Learn More
IPO Readiness
32% of companies report material weaknesses from SoD issues. Pathlock automates stronger controls to ensure a smoother IPO.
Learn More
NHI Governance
In many companies, non-human identities outnumber users 20:1. Pathlock applies rigorous controls to both to ensure security and compliance.
Learn More
SAP Cybersecurity
Protect your SAP environment from development to deployment. Pathlock secures SAP applications and data to reduce the risk of a breach
Learn More
Be Audit-Ready, Without the Additional Stress
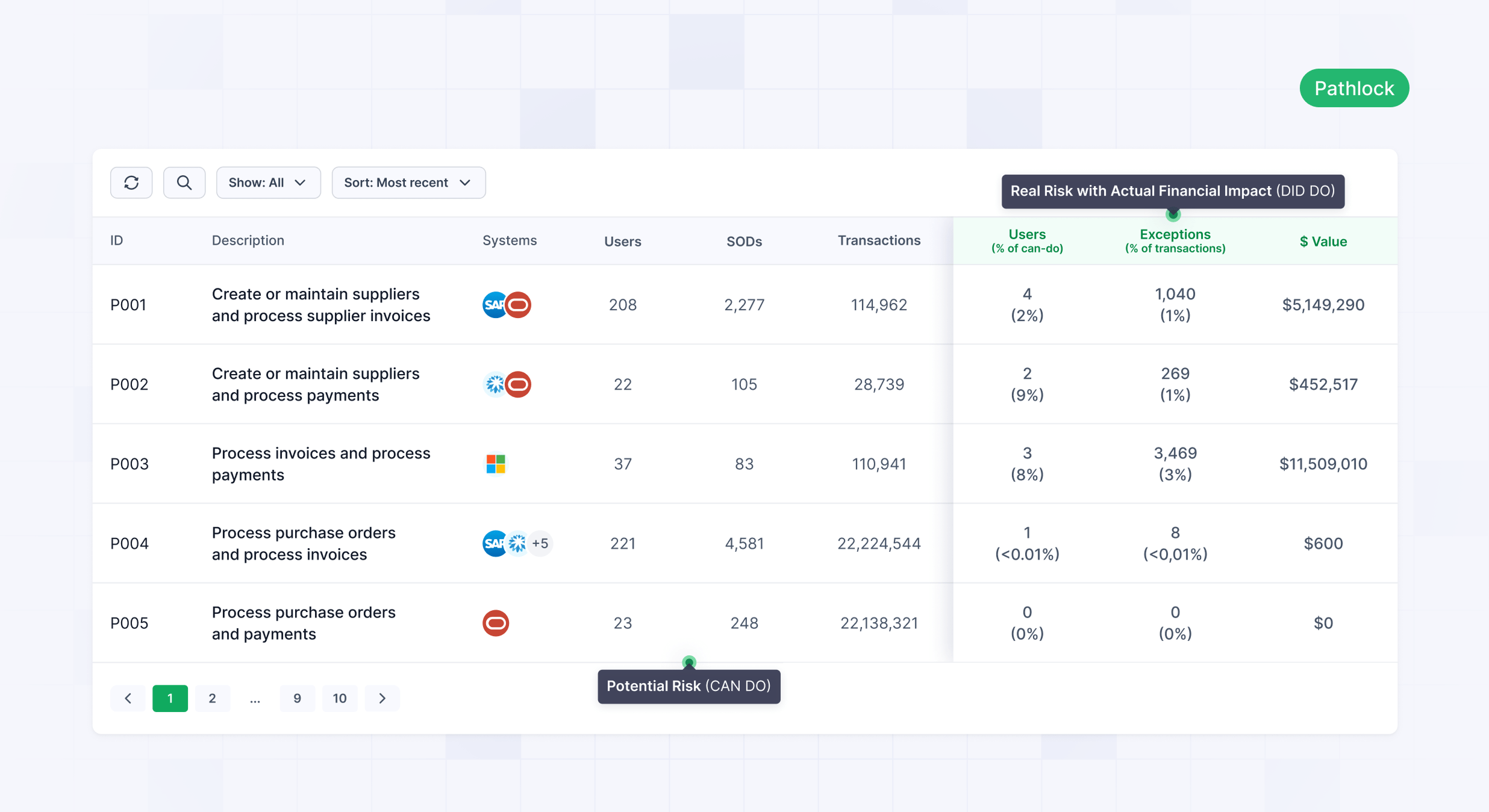
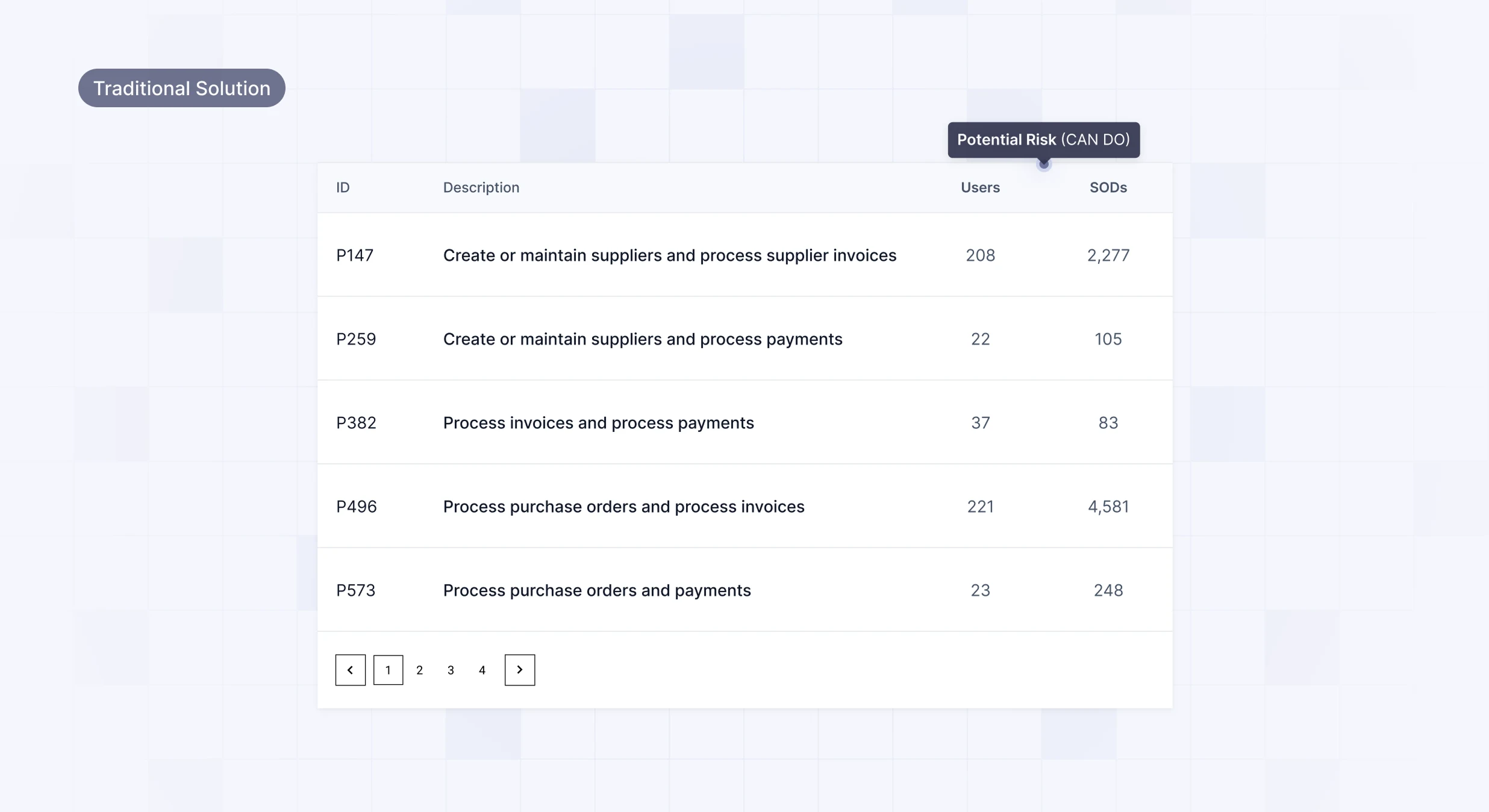
Overcome the Limitations of Traditional SAP Access Control Solutions Putting Your Compliance at Risk

Manage Cross-Application Risk for SAP and Beyond
Discover how Pathlock identifies real access risks across SAP applications and helps you prioritize remediation with fine-grained SoD analysis.

Automate UARs Tailored to Your Needs
See how Pathlock automates user access reviews, identifies risky entitlements, and delivers actionable insights to enforce least privilege.

Leverage an Audit-Proof Firefighter Process
Learn how Pathlock manages time-bound elevated access, logs privileged activity, and prevents standing privileges across your systems.

Simplify Your GRC Process with Out-of-the-Box Reports
Discover how Pathlock’s out-of-the-box reports, complete with audit trails and risk quantification, help you stay ahead of auditor requests.

Layer Compliance Across Your Landscape
See how Pathlock integrates with Microsoft Entra, SailPoint, SAP IDM, Oracle IDM, and other identity solutions to ensure compliant access to critical business systems.
Flexible Deployment Options to Fit Your Needs
Connectors
for SAP ERP
Fine-grained identity governance starts with fine grained connectors.
Visit Connector StudioSAP ERP and SAP S/4
SAP ERP is an integrated software system that helps businesses manage core processes like finance, supply chain, ma...
SAP S/4HANA Public Cloud
SAP S/4HANA Public Cloud is a cloud-based ERP solution that provides real-time data processing and AI-driven automa...
 >
>
