Agility is the name of the game in today’s ERP data security landscape. Organizations are being challenged to detect threats as they happen, quickly address vulnerabilities, and continuously improve their security posture while protecting crucial ERP data as well as their overall business. One strategy that is helping organizations become more proactive is aligning with an adaptive security model.
Focused on operationalizing agile, context-aware, and adaptive technologies, an adaptive security model enables organizations to strengthen security and leverage automation for continuous improvement.
What is Adaptive Security?
Adaptive security is an approach to managing security that analyzes behaviors and events to protect against and adapt to threats before they happen. With an adaptive security architecture, an organization can continuously assess risk and control effectiveness monitoring and automatically provide proportional enforcement that can be dialed up or down to fit its needs.
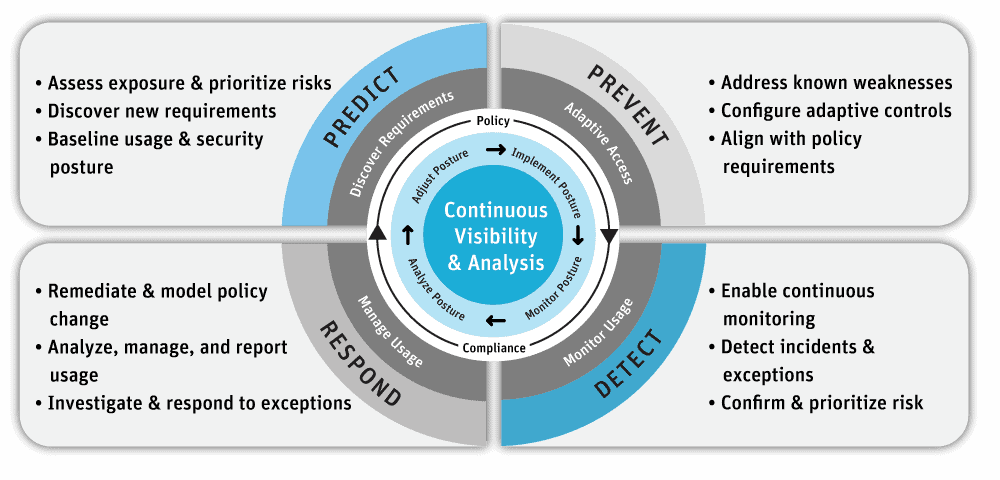
Figure 1: Adaptive Security Architecture
You’ll note that there are four stages of an adaptive security architecture: Prevent, Detect, Respond, and Predict. These stages help organizations transform the old static, roles-based approach to ERP data security to a continuous monitoring and risk-adaptive approach. Zero trust is a core concept to adaptive security, which promotes continuous monitoring and analysis as a starting point, enables rapid detection of behavioral anomalies, and permits rapid responses to quickly stop and resolve security incidents.
Seven Imperatives for an Adaptive Security Architecture
According to Gartner, supporting digital business transformation in an environment of advanced threats requires a new approach for all facets of security. Security and risk management leaders can use these seven imperatives of an adaptive security model to embrace the opportunities and manage digital business risks. Each imperative is Gartner’s recommended capability required of your ERP security, risk & compliance solution to enable the security model.
- Replace One-Time Security Gates with Context-Aware, Adaptive, and Programmable Security Platforms
Organizations need to replace the initial one-time, yes/no risk-based decision at the main gate to their systems (typically managed by a static authentication and authorization process) with a continuous, real-time, adaptive risk and trust analysis of user anomalies with context-aware information across the platform. Context-aware security (also known as attribute-based access controls or ABAC) uses situational information, such as identity, geolocation, time of day, or type of endpoint device. - Continuously Discover, Monitor, Assess, and Prioritize Risk — Proactively and Reactively
Risk events are fluid and require constant identification, analysis, prioritization, monitoring, and response after the initial login assessment. This should include a combination of proactive and reactive capabilities. For example, if a user attempts to download a large amount of sensitive data, you need the ability to detect and prevent this action if it’s considered inappropriate. Again, the use of ABAC can provide organizations with preventative controls at the business process, transaction, and master data level. - Perform Risk and Trust Assessments Early in Digital Business Initiatives
This imperative focuses on early risk assessment, meaning performing risk and trust assessments early in the process execution. - Instrument Infrastructure for Comprehensive Full Stack Risk Visibility, Including Sensitive Data Handling
This is a continuous risk assessment recommendation across the full tech stack and data handling to enable adaptive security decisions. - Use Analytics, AI, Automation, and Orchestration to Speed the Time to Detect and Respond and to Scale Limited Resources
This imperative recommends using artificial intelligence, machine learning, analytics, and automation to increase the efficiency and effectiveness of risk detection, analysis, and response capabilities. - Architect Security as an Integrated, Adaptive Programmable System, Not in Silos
Avoid silos! Organizations shouldn’t perform risk assessments in individual isolated silos. Instead, aggregate continuous risk assessments provide a more accurate view of the organization’s risk exposure. - Put Continuous Data-Driven Risk Decision Making and Risk Ownership into Business Units and Product Owners
This imperative encourages better transparency and decision-making through better data-driven risk visibility to the business unit leaders for their own decision-making.
How Pathlock Security Helps Organizations Achieve Adaptive Security
The problem we help companies overcome: In its current form, the static data protection approach utilized by most organizations lacks the effectiveness required to manage today’s complex challenges. Without an accurate picture of risk exposure in their organization, security administrators protect data the only way they can – with restrictive measures under the principle of least privilege and zero trust.
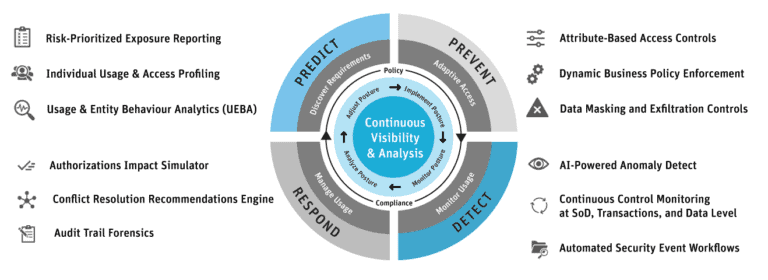
Here’s how Pathlock Security’s capabilities align with the Gartner adaptive security model. The Gartner adaptive security model is illustrated with the Pathlock Security solution capabilities aligned with their Predictive & Discovery Requirements, Preventative & Adaptive Access, Detective & Monitor Usage, and Respond & Manage User capabilities.
Five Ways Pathlock Security Helps Improve ERP Data Security
Organizations are being challenged to protect access to sensitive and confidential data while improving their ability to analyze security data and detect attacks in progress. Here are five ways that Pathlock Security can help your organization meet these challenges:
- The capabilities of the Pathlock Security solution align with Gartner’s Seven Adaptive Security Imperatives.
- Pathlock offers context-based access controls that can prevent, detect, and respond to user anomalies at the business process, transaction, and data level.
- Pathlock enables continuous monitoring and real-time reporting of user anomalies.
- Pathlock offers artificial intelligence, machine learning, and automation to increase the efficiency and effectiveness of your risk detection, analysis, and response capabilities.
- Pathlock can automate the enforcement of your policy requirements at the business process, transaction, and data level.
Contact Pathlock today to learn how our zero-trust solutions can anchor your adaptive security architecture and improve your ERP data security.