Application governance encompasses the policies and rules enterprises adopt to manage their applications. The objectives of application governance are to increase data security, manage risks, and keep applications running smoothly.
Application governance helps ensure that development teams properly plan and manage various aspects of an application, including how they deploy assets, integrate systems, and secure data.
An application governance program ensures that the complex application environment meets the organization’s security policies, best practices, and compliance requirements.
We’ll focus on two critical aspects of modern application governance: cloud governance and mission-critical application governance, with a special focus on SAP applications.
This is part of a series of articles about identity and access management.
5 Principles of Cloud Application Governance
Cloud application governance frameworks leverage existing practices to ensure secure, compliant, and efficient cloud operations.
1. Security and Compliance Management
Cloud governance frameworks utilize common enterprise security practices, including risk assessment, data encryption and key management, identity and access management, application security, and contingency planning. A governance program frames these information security practices around business goals and regulatory requirements.
2. Financial Management
Cloud computing can help lower costs, but it requires financial management to ensure costs remain on budget. Here are several ways to prevent wasteful spending and cost overruns:
- Financial policies—cloud governance policies should include financial policies that define resources for each project and workload. Set up processes to alert when budget consumption thresholds exceed so that you can control costs.
- A budget—use a budget to define a specific allotted quota for each project and department.
- Cloud expense reporting—most cloud vendors offer cost reporting tools. Still, organizations implementing multi-cloud or hybrid-cloud environments may need third-party tools to bridge the reporting gap between accounts and providers.
3. Operations Management
Cloud operations include tuning, delivering, monitoring, and optimizing workload performance in the cloud. It is critical to define a cloud operations management process for your service deployment, including the following:
- Define resources assigned to each service.
- Define and enforce access controls for all services and associated resources.
- Implement continuous monitoring to ensure resources are delivered.
- Determine requirements and parameters for deploying code to production.
Cloud operations management helps ensure predictable costs, prevent shadow IT, and reduce unexpected spikes to a minimum.
4. Data Management
Cloud platforms enable storing and processing large amounts of data and flexibly delivering it to all people, departments, and applications that require it. However, the complexity of data management increases even as data collection capabilities improve, making cloud data management a crucial aspect of governance strategies.
A governance strategy provides clear guidance on managing various kinds of data. It typically involves using a classification system to classify all data and prioritizing it according to confidentiality and accessibility requirements. Encrypting data at rest and in transit by default is another basic measure defined in most governance strategies.
5. Performance Management
Cloud computing performance management helps monitor application and infrastructure resources to ensure the desired level of service delivery and efficient cloud infrastructure usage. Application performance metrics are usually application-specific.
Common metrics include the number of connected users, the number of database transactions per epoch, and the latency of retrieving data, calling API functions, or loading web pages. Performance management tools can generate alerts to notify administrators and teams when services do not behave as expected.
Learn more in our detailed guide to application governance (coming soon)
Mission-Critical Application Governance: Focus on SAP
In many large organizations, SAP business applications perform mission-critical operational tasks. Let’s explore how to implement a governance strategy for these mission-critical workloads.
Within an SAP ecosystem, it is common to organize a governance strategy using SAP-specific solutions. SAP provides Governance, Risk, and Compliance (GRC) as a suite of solutions and products that help you manage SAP environments in a way that minimizes risk and reduces compliance costs. SAP GRC addresses four pillars of application governance, illustrated below and detailed in the following sections.
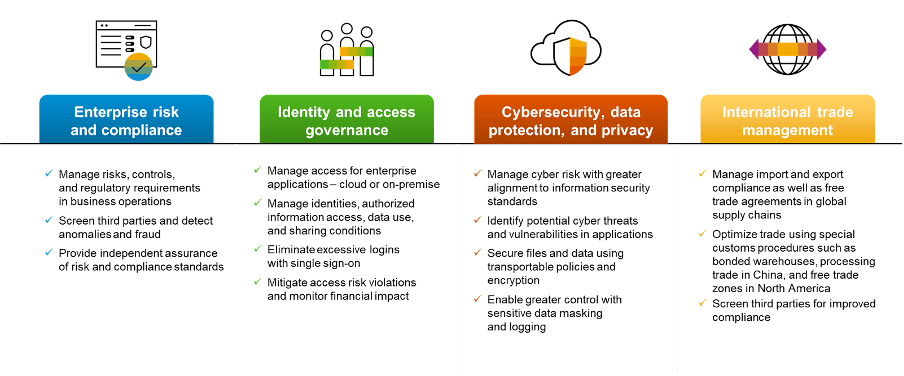
Enterprise Risk and Compliance
This area of SAP GRC helps connect operations, risk management, compliance, and internal auditing. It allows organizations to:
- Document and monitor risk and compliance requirements.
- Align risk management and controls with business goals.
- Develop policies and evaluate compliance with those policies.
- Document security controls and procedures for incident response and recovery.
- Auditing business and security risks and existing controls.
- Achieving awareness of security concerns at the senior management and board level.
Identity and Access Governance
This area of SAP GRC helps manage system accounts to ensure strong, secure authorization. SAP identity and access governance solutions enable organizations to monitor and manage identities and control who has access to what information and processes within the organization, both for cloud and on-premises. It enables:
- Central identity management and automated provisioning of accounts.
- Management of enterprise application roles and attributes as part of RBAC/ABAC access frameworks.
- Provide single sign-on (SSO) to eliminate duplicate logins and improve user experience.
- Reduce audit costs and make it easier to identify access violations.
- Provide monitoring, log review, and automated workflows for privileged accounts.
Cybersecurity, Data Protection, and Privacy
This area of SAP GRC can assist an organization with threat monitoring, data control, and privacy management. It can improve the security posture of critical applications by:
- Aligning applications with information security standards to better manage cyber risk.
- Identifying application threats with real-time pattern detection at the application layer.
- Masking sensitive data to avoid unauthorized access and logging all access to sensitive data.
- Enforcing policies for accessing data in public clouds and transferring data to the cloud.
International Trade Management
This area of SAP GRC enables organizations to triage their trading partners, reduce the risk of fines, and expedite inbound and outbound customs clearance. It can help an organization:
- Automate import/export trade processes and identify concerns with third parties to improve compliance.
- Leverage free trade agreements to reduce costs.
- Manage customs procedures such as electronic declaration, bonded warehouse, and foreign trade areas.
- Centralize international transactions on one platform to improve consistency across global logistics operations.
Application Governance with Pathlock
GRC is a hassle, with seemingly endless amounts of manual work piling up by the day. Organizations typically have 200+ key internal controls to prove each type of compliance, and each control takes 40 or more hours to test. Furthermore, testing on these controls may only be done once a year. This is an error-prone process that only looks at 3-5% of the activity in a given enterprise.
Pathlock shifts organizations towards a continuous compliance approach, which proactively monitors controls and reports on violations of those controls in real-time. Organizations can have complete visibility of their risk and compliance status at all times so they are always prepared for the next audit.
Complete Visibility
Pathlock radiates GRC and IRM information to the most critical tools in your landscape for real-time status on your key controls. Pathlock integrates with ServiceNow, MetricStream, Archer, SailPoint, Okta, SAP GRC, and more.
Comprehensive Rulebook
Pathlock’s catalog of over 500+ rules, Pathlock can provide out-of-the-box coverage for controls related to SOX, GDPR, CCPA, HIPAA, NIST, and other leading compliance frameworks.
Real-time Risk Mitigation
Pathlock allows users to quickly investigate and respond to potential risky transactions by reviewing access, deprovisioning users, forcing 2FA, or even allowing Pathlock to respond intelligently in real-time, terminating suspicious sessions and blocking transactions.
Out-of-the-Box Integrations
Pathlock’s out-of-the-box integrations have your key business applications covered. Monitor and enforce controls across SAP, Oracle, Salesforce, Workday, NetSuite, Dynamics365, and more.
Lateral SOD Correlation
All entitlements and roles are correlated with a user’s transactional behavior, consolidating activities and showing cross-application SODs between financially relevant applications.
Continuous Control Monitoring
Pathlock identifies the largest risks by monitoring 100% of financial transactions from applications like SAP in real-time, surfacing violations for remediation and investigation.
Interested to find out more about how Pathlock is changing the future of GRC? Request a demo to explore the leading solution for enforcing compliance and reducing risk.



