SAP IDM End of Life Timelines
SAP is shifting its IDM security roadmap by moving away from the legacy IDM tool and adopting a cloud-first identity governance model. The following are the two important timelines pertaining to the end of life for SAP IDM.
SAP IDM End of Mainstream Maintenance in 2027
According to SAP’s official channels, mainstream maintenance for SAP Identity Management 8.0 will end on 31st December 2027,
SAP IDM End of End of Extended Maintenance in 2030
SAP IDM extended maintenance will be available until 2030 at an additional cost.
SAP Identity Manager Transition to Microsoft Entra ID as the Enterprise IGA Direction
Migration from SAP IDM is not a ‘like-for-like’ product replacement. SAP is transitioning its IGA strategy by partnering with Microsoft, positioning Microsoft Entra ID as the primary solution for enterprise-wide identity lifecycle management. At the same time, SAP Cloud Identity Services handles the specialized integration within the SAP ecosystem.
SAP is also moving away from continuous development of the on-premises Identity Governance and Administration (IGA) tool. Rather than a simple technology refresh, this is a broader shift toward cloud-centric identity, access governance, and compliance models, with Microsoft Entra ID as the enterprise-wide focus. By moving identity logic out of custom IDM scripts and into a standardized governance layer like Pathlock or Microsoft Entra ID, organizations support the ‘Clean Core’ initiative, reducing custom technical debt within the ERP and ensuring easier future upgrades to S/4HANA. Let’s take a close look at the implications of this standard and the extended end of maintenance for SAP IDM.
Recognized in Gartner® Market Guide for IGA 2025
What are the implications of SAP End of Standard and Extended Maintenance?
SAP follows a standard software lifecycle policy, but this transition means that there will be no new version. Unlike previous cycles, there is no IDM 9.0. SAP Identity Management 8.0 is the final functional release, making the transition to a new architecture mandatory rather than an upgrade. As it is the final version, the migration window is narrowing, as SAP has set official deadlines for IDM 8.0.
Until December 31, 2027, the end of mainstream maintenance, SAP will provide full support, including bug fixes, security patches, and support for new browser versions and operating systems.
Organizations that cannot migrate by 2027 can use the extended maintenance program, typically at increased licensing costs, which focuses on critical issues; no new features or enhancements will be developed or supported.
Customers are encouraged to plan migrations well ahead of these deadlines to avoid risks and disruptions to business activities. According to experts, a typical IAM migration is a complex, long-running project. It takes between 18 and 36 months for a large organization. In February 2024, SAP officially announced the sunsetting of SAP IDM, providing the market with a clear timeline for the 2027 mainstream maintenance cutoff, giving organizations ample time to migrate. However, starting the planning phase in 2026, at the time of this article’s publication, is considered critical to avoid the 2027 cutoff date, reduce risk, and control costs.
What is Changing in the SAP IAM Landscape?
SAP IDM 8.0 is a Java-based solution running on SAP NetWeaver that relies on the Virtual Directory Server (VDS) for LDAP-based integrations and a central SQL database for its Identity Store. Modern cloud-native solutions replace this complex, script-heavy infrastructure with API-driven (REST/SCIM) connectivity.
The modern SAP IAM landscape includes Cloud- and SaaS-based applications, System for Cross-domain Identity Management (SCIM), and REST APIs, with a focus on configuration over coding, especially no-code/low-code workflow builders, enabling faster deployments and easier updates.
SAP customers don’t just run SAP ECC; they have adopted a mix of on-premises and cloud S/4HANA, SAP SuccessFactors, SAP Business Technology Platform (BTP), and hybrid SAP environments, and they integrate non-SAP SaaS applications such as ServiceNow and Salesforce. SAP IDM struggled to integrate and manage cloud-native features such as Just-in-Time (JIT) access provisioning, a standard modern security requirement.
Additionally, cloud-based identity management solutions manage a broader set of identities, including partners, contractors, non-human identities (e.g., bots, IoT devices, and service accounts), and employees.
SAP did not announce a direct successor to SAP IDM within its product line; instead, it encouraged customers to focus on its cloud services, SAP Cloud Identity Services (CIS), or partner services such as Microsoft Entra ID. Microsoft has already begun offering migration guidance to SAP customers, serving as a preferred bridge for the SAP identity lifecycle.
SAP’s Identity Management Direction to Cloud Identity Services
SAP Cloud Identity Services serves as a hub for all SAP cloud environments, providing a seamless user experience across SAP ecosystems and supporting modern security standards, including Security Assertion Markup Language (SAML), OpenID Connect (OIDC), System for Cross-Domain Identity Management (SCIM), and X.509. SAP Cloud Identity Services, such as Identity Authentication (IAS), Identity Provisioning (IPS), and Identity Directory (IDS), are the center of SAP’s cloud Identity and Access Management strategy, simplifying authentication and provisioning across SAP cloud applications.
- Identity Authentication Service functions as an identity provider to an existing corporate IdP, such as Okta or Microsoft Entra ID. It manages Single Sign-On, self-service password management, and Multi-Factor Authentication.
- Identity Provisioning (a service of SAP Cloud Identity Services) acts as the technical connector, synchronizing identities between SAP and non-SAP systems via the SCIM standard, effectively replacing the connectors previously managed by the SAP IDM Identity Center.
- Identity Directory Service serves as a central repository for keeping user profiles and attributes within the SAP cloud, enabling consistent user data synchronization in different SAP applications.
- Authorization Management Service enables organizations to manage access policies to resources based on user values or business object attributes.
SAP Cloud Identity Access Governance (IAG)
SAP IDM focuses on the identity lifecycle, while SAP Cloud Identity Access Governance (IAG) also provides governance and compliance services. It is primarily positioned as a cloud access governance service rather than a replacement for full SAP IDM. SAP IAG provides a self-service portal for users to request access and for managers to certify whether users still need their current access. It also offers access request workflows, role design, and a real-time access analysis service based on segregation of duties (SoD) to ensure users do not have conflicting roles, e.g., creating and approving vendors.
Role of Partners
SAP explicitly informed customers that it is not building a replacement for complex, custom-scripted SAP IDM workflows, and emphasized that they should integrate with partner IAM and governance solutions to address their complex lifecycle, compliance, and hybrid governance needs. Partners such as Microsoft Entra ID are strategic partners and recommended solutions for the entire enterprise. Customers are expected to assemble future-state architectures using SAP services and other specialized partners, such as Pathlock Cloud, or to engage SAP implementation partners, including PwC, Deloitte, and EY.
Pathlock Cloud as an SAP IDM Alternative
Why Organization should Migrate to Pathlock Cloud?
Pathlock is an official SAP strategic partner for organizations transitioning away from SAP Identity Management following its end-of-life announcement. It specializes in Identity Governance and Administration (IGA) and Application Access Governance (AAG). Pathlock is designed to fill the gap between on-premises identity management and modern cloud governance. Pathlock provides a deep governance layer for the granular complexities of SAP security, such as transaction codes, objects, and authorizations. It helps organizations to govern access and compliance across SAP and non-SAP environments during or after SAP IDM retirement.
The following is a quick overview of how Pathlock Cloud helps organizations with more granular and converged identity management with cross-application security.
Identity Governance Management by Pathlock
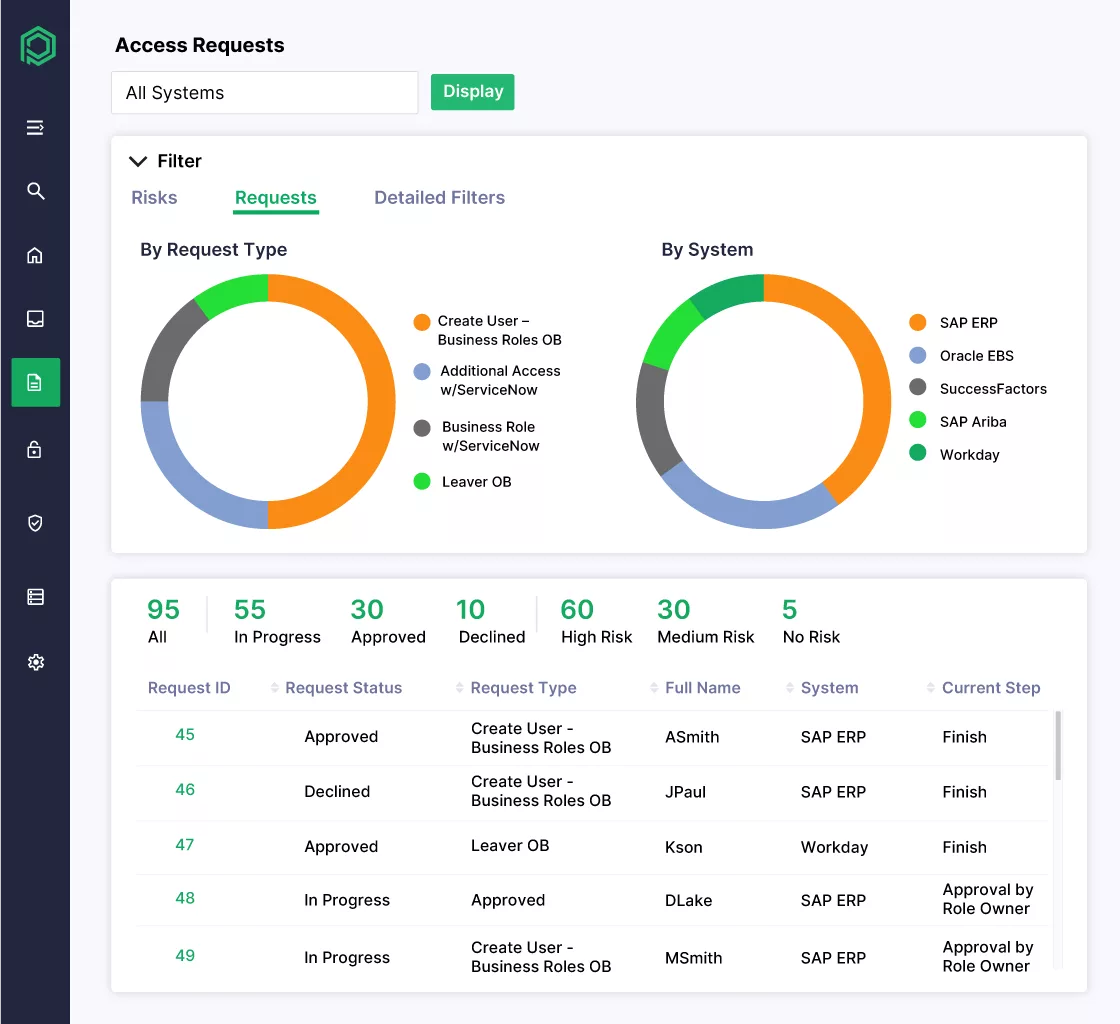
Pathlock Cloud IGA solution automates user creation and maintenance across SAP ECC, S/4HANA, and BTP, as well as non-SAP environments such as Oracle, Workday, and Salesforce. It offers out-of-the-box Joiner/Mover/Leaver workflows to manage user onboarding, transfers, offboarding, and immediate access revocation upon user termination. Pathlock offers a user-friendly self-service portal for access requests and approvals. The system performs proactive SoD analysis before the request reaches an approver, preventing access conflicts.
Application Access Governance (AAG)
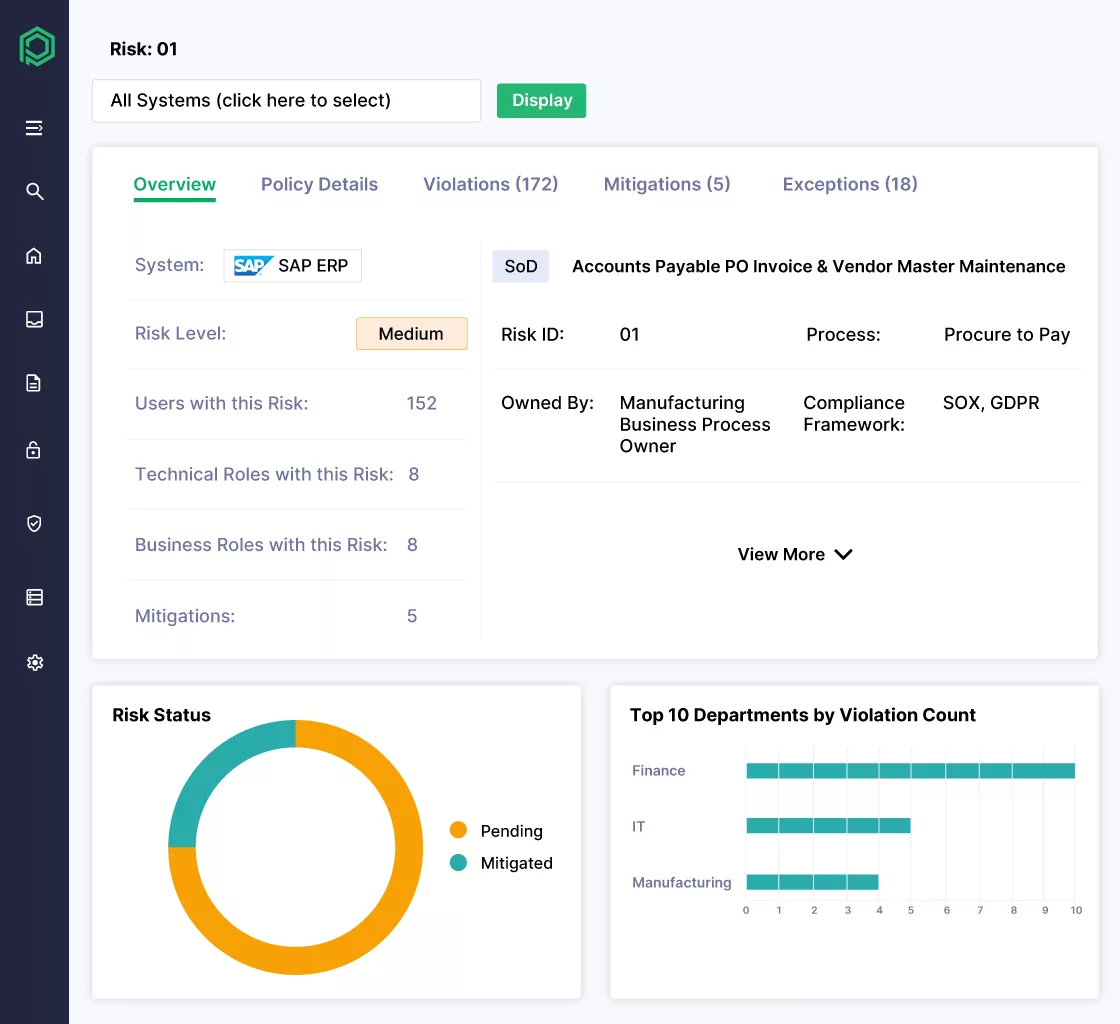
Pathlock’s Application Access Governance module provides a library of preconfigured Segregation of Duties rules for analysis that detect cross-application SoD risks and conflicts to enforce least-privilege access. AAG also monitors sensitive access, e.g., who is accessing critical data or important transactions, and then triggers alerts for respective teams for the anomalous behavior. Pathlock offers elevated/emergency access management, often used as Firefighter, a feature that provides controlled time-based access to manage critical situations with a fully audited workflow and privileged access.
Centralized Dashboards
Pathlock Cloud offers centralized dashboards for different audiences, including auditors, security teams, and business process owners. Auditors can generate one-click reports for compliance regulations such as GDPR, SOX, and HIPAA. The business owner dashboard simplifies complex SAP roles into business roles, enabling managers to understand them during access reviews and certifications easily.
How Pathlock Cloud Offers Converged Identity Management?
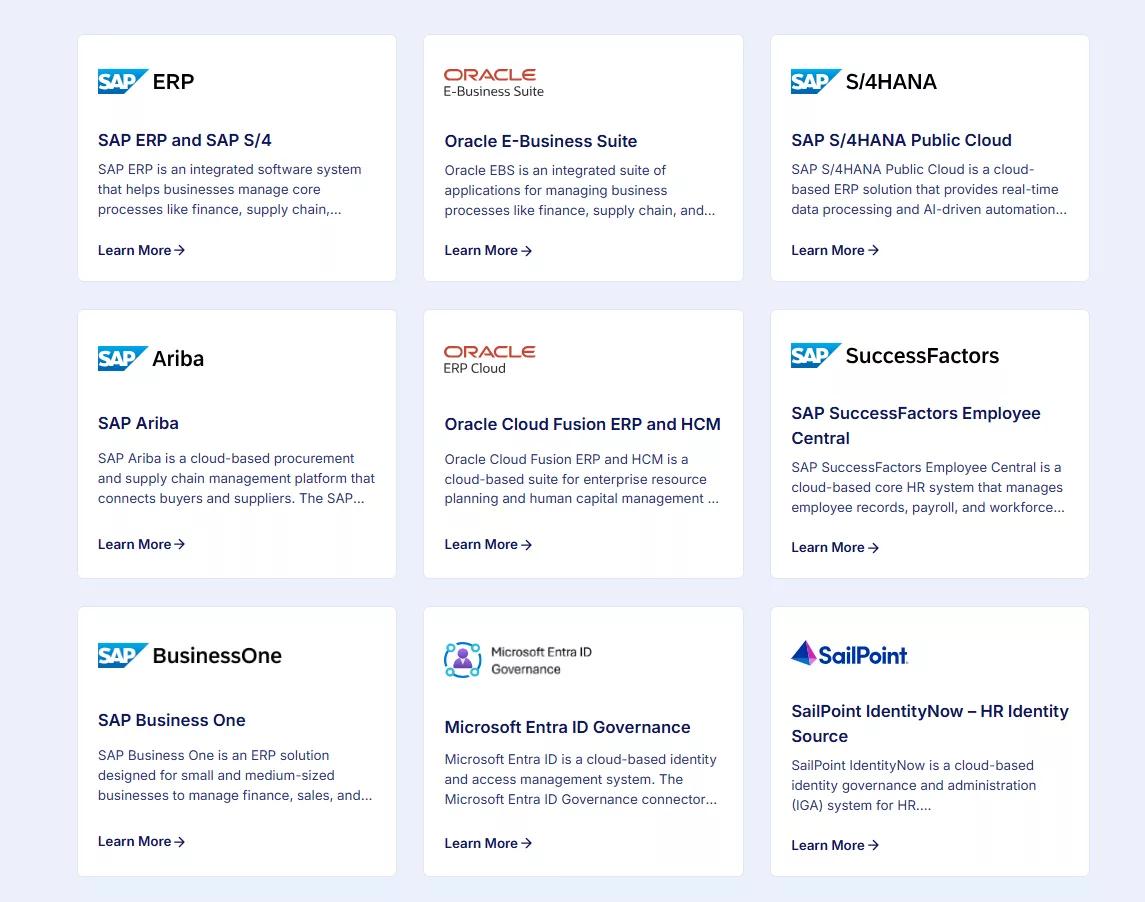
Pathlock Cloud offers converged Identity management with its extensive connector library. The following are most significant integrations in Pathlock’s connector library, enabling the organization to develop a smoother SAP IDM migration Roadmaps considering the end of standard and extended maintenance in 2027 and 2030.
SAP Integrations
Pathlock Cloud is designed to serve as the connective tissue for identity governance; its deep-integration model focuses on granular connectivity with SAP environments, for example, by extracting data at the authorization object and transaction code levels.
- Pathlock provides integration for SAP ECC and SAP S/4HANA private edition and supports a complex ABAP-based authorization model, reads roles hierarchy and authorization objects for real-time SoD analysis, and automated user and role provisioning.
- Pathlock uses standard APIs for communication, user management, SoD, access analysis, access certification, tracking, auditing, Firefighter session management, and roles management with SAP S/4HANA Public Cloud integration.
- Pathlock integrates with SAP BTP subaccounts for developers and administrators’ access, ensures access governance for BTP-hosted services and applications, along with SoD, access analysis, access certification, tracking, auditing, Firefighter session management, and roles management.
- Pathlock integrates with SAP SuccessFactors, used as an identity source for employee lifecycle, and automatically triggers joiner or leaver workflows for new hires and termination across connected SAP and non-SAP applications, along with SoD, access analysis, access certification, tracking, and auditing.
Non-SAP and Enterprise Integrations
Pathlock also provides integrations with non-SAP and other enterprise applications, ensuring identity governance is not limited to SAP systems.
- Pathlock provides connectors for Microsoft Active Directory and Entra ID, with automated account creation and group membership management to enable Single Sign-On access and alignment of corporate identities with application-level accounts, along with SoD, access analysis, certification, and elevated session management.
- Pathlock offers integration with ServiceNow for ITSM-based request workflows and fulfillment, which enables users to directly request access to SAP from within the ServiceNow service portal, with proactive SoD checks and automatic access provision upon approval.
- Pathlock offers a connector framework for the applications for which an out-of-the-box connector is not available, such as SCIM, SOAP, and REST APIs for SaaS applications like Slack, Workday, or Salesforce, direct database-level access using JDBC or ODBC, and manual import/export integration for flat-file systems.
Discover more on Pathlock’s connector’s library below:
How to Phase Migration Approach from SAP IDM to Pathlock Cloud?
Organizations moving away from IDM should use a phased approach to minimize risks, build skills and tools incrementally, and ensure compliance is maintained during the transition of their identities and access governance to another solution. SAP and Pathlock experts recommend a staged migration to Pathlock Cloud, allowing organizations to continue business operations without disruption. It is divided into three logical phases to support early compliance as SAP IDM is retired gradually.
Phase 1: Visibility and Risk
This phase focuses on getting visibility into existing systems and performing risk assessment before migrating provisioning workflows to Pathlock Cloud. This phase is often referred to as audit and cleanup.
- Integrate your existing SAP systems, such as SAP ECC, SAP S/4HANA, and SAP SuccessFactors, and key non-SAP business systems, e.g., Entra ID or Workday, to Pathlock Cloud using their out-of-the-box connectors. The recommended approach is to make this connectivity read-only or one-way.
- Run baseline SoD analysis, conduct user access certification, and sensitive access reviews to detect conflicts across applications, for the risk not visible in SAP IDM, and generate an audit-ready access certification report for compliance support.
- Use Pathlock’s dashboards to identify current access state, roles, and role bloat. This will help identify excessive permissions that high-risk users may have accumulated over time.
- Delete unused roles and revoke access for orphaned accounts using Pathlock’s insight, before transitioning them to the new system.
Phase 2: Lifecycle and Provisioning
This phase focuses on the SAP IDM’s core identity lifecycle engine shift to Pathlock.
- Migrate Joiner/Mover/Leaver workflows and logic from SAP IDM to Pathlock Cloud. Pathlock uses a configuration-based workflow engine instead of SAP IDM’s custom JavaScript.
- Enable governed provisioning for newly hired users, such as in SAP SuccessFactors, Pathlock Cloud automatically provisions user accounts and access, evaluated against policies and rules, in SAP and non-SAP connected systems.
- Identify and retire any complex, custom SAP IDM scripts and replace them with Pathlock Cloud’s business rules and configuration-based workflows.
Phase 3: Advanced Governance
This final phase focuses on implementing advanced governance, including robust security and continuous compliance.
- Leverage Pathlock’s role mining capabilities, analyze users’ activities, and design automated, least privilege roles.
- Transition from manual break-glass IDs to Pathlock’s automated Elevated Access Management (Firefighter) capabilities, which provide secure and audited sessions to admins for performing emergency tasks.
- Move away from periodic audits to continuous control monitoring, which provides continuous compliance and configuration changes. Pathlock monitors transactions in real time, detects when a user executes conflicting transactions, and generates a compliance report.
How can SAP IDM Concepts be Mapped to Pathlock Cloud?
It is crucial for organizations transitioning from SAP IDM to understand and map the data structures of their existing objects to the modern Pathlock Cloud architecture to ensure a successful migration. Following is the list of concepts that are being mapped from SAP IDM to Pathlock Cloud:
- Identity Stores and Visibility
- Role and Identity Mapping
Let’s take an in-depth look at each of these
Identity Stores and Visibility
The Identity Store, also referred to as a database in SAP IDM, stores data on objects, role assignments, and historical logs. Manual querying and maintenance are needed to retrieve that data.
| SAP IDM | Pathlock Cloud |
|---|---|
| Stores user attributes, roles data, entry types, and history of tasks or audit data in the identity store, managed using SQL and JavaScript; audit data is stored in history tables requiring complex queries to manipulate. Technical administrators can view and understand it, but end users often struggle to find and interpret this data | Centralizes data from all connected systems (SAP and non-SAP) into a unified identity repository, providing a single pane of glass that shows who has access to what, rather than raw database tables. It also provides a complete, searchable history of attribute and access changes, as well as compliance violations, across the entire enterprise |
Role and Identity Mapping
SAP IDM stores object technical schemas in the MX_ format, such as MX_PERSON, MX_ROLE, or MX_PRIVILEGE. Pathlock maps them directly to its functional components.
MX_PERSON → Global Identity
| SAP IDM | Pathlock Cloud |
|---|---|
| MX_PERSON represents an individual user in the SAP IDM identity store. | Pathlock employs identity correlation to link multiple accounts, such as an SAP user ID, a Salesforce login, and an Active Directory account, to a single global identity. This enables security teams to see a user’s total access across enterprise applications through comprehensive access governance, rather than seeing different accounts across different systems. |
MX_ROLE → Business Roles
| SAP IDM | Pathlock Cloud |
|---|---|
| MX_ROLE is used in SAP IDM to group multiple privileges or other roles into a single assignment unit for access provisioning. | Pathlock Cloud uses Business roles to bundle entitlements, not only in SAP but across all target systems. These roles are designed to improve understanding among business managers, such as the Accounts Payable Clerk role. Pathlock can also bundle entitlements across platforms, such as SAP S/4HANA, ServiceNow groups, or a specific SharePoint folder |
.
Technical Roles → Fine-Grained Entitlements
| SAP IDM | Pathlock Cloud |
|---|---|
| Privileges are managed using the MX_PRIVILEGE entity type and are often treated as role names in SAP IDM, such as ABAP roles, system groups, or profiles. In SAP IDM, MX_PRIVILEGE typically represents a single backend assignment (like an ABAP role or a group). | Pathlock Cloud goes a level deeper, decomposing these privileges into fine-grained authorizations (Transaction Codes and Authorization Objects) to perform real-time Segregation of Duties (SoD) analysis before the role is ever assigned. |
How Pathlock Cloud aligns Access Lifecycle Management with GRC?
SAP customers moving away from SAP IDM are increasingly seeking a single platform that combines Identity Governance (IGA) and Governance, Risk, and Compliance (GRC) functions. The challenge is not just provisioning users and their access; the problem is ensuring they remain compliant throughout their tenure with the organization. Pathlock Cloud offers all these capabilities, aligning identity lifecycle with deep risk management, governance, and compliance, serving as an alternative platform to SAP IDM and SAP GRC Access Control.
Pathlock Cloud offers user-friendly self-service features, including access requests with automated SoD analysis to streamline risk and approval workflows. When a user access request is triggered in the Pathlock portal, the system calculates the impact of the new permissions request on existing user permissions. It performs SoD analysis before the request reaches an approver. Automated approval workflows can be configured for risk levels. Low-risk requests can be configured for auto-approval, and high-risk requests can be routed to multiple stakeholders, including role owners, security officers, and managers.
Traditionally, access reviews were conducted manually using spreadsheets, email, or reports, and were periodic. Pathlock provides automated access reviews and certifications, and generates review tasks for managers via dashboards to provide access insights for their direct reports. Pathlock generates risk-based reviews rather than reviewing every user through certifications. These reviews are based on department change events, user activity within the last 90 days, or high-risk assignments. Additionally, if a manager revokes a user’s access during access review, Pathlock automatically deprovisions access across all targeted systems, ensuring continuous compliance.
Pathlock Cloud is specifically designed to cover the functional footprint of both identity lifecycle and continuous compliance. It can either bridge or replace SAP customers’ reliance on SAP IDM and SAP GRC Access Control by providing provisioning, SoD, and firefighter use cases, depending on the organization’s scope and strategy, such as the need for cross-application governance across SAP and non-SAP applications.
External Identities and Contractors
Another unique security challenge is managing external identities, such as partners, vendors, and contractors. Identity governance solutions must support both internal and external identities. These external users sometimes need high-level access to SAP systems, but they do not exist in either the HR system or the SAP system, and they may not exist in all connected systems. Pathlock Cloud can apply the same governance to all external identities as it does to internal employees. Pathlock Cloud aggregates external identities from multiple connected systems, such as HR databases and vendor management systems, and provides centralized visibility within a single governance view. External identities can be provisioned in the same way as internal employees; organizations can design approval workflows for them, and they are subject to the same SoD analysis during the access request and approval process.
Another common security gap is orphaned contractor, vendor, and external user accounts that remain active or retain access to resources even after the project has ended. Pathlock Cloud offers an automated risk-aware joiner and leaver process for external identities to eliminate this risk. It can ingest contract end dates at the attribute level. As the date approaches, the system automatically triggers the deprovisioning workflow, which locks the user, deletes the account, and revokes access from all connected applications. Revocation can be triggered by the project lifecycle, such as a status change in project management systems, or by a manual request from the project coordinator or sponsor.
Pathlock separates authentication from governance, e.g., confirming who the user is and verifying what that user can do in any system, enabling organizations to use their existing identity provider to manage identities and use Pathlock’s governance capabilities to manage SAP and non-SAP authorizations. Okta, Microsoft Entra ID, or Ping Identity can be used for authentication. Pathlock supports OpenID Connect (OIDC) and SAML 2.0 to enable this. When IdPs manage login, Pathlock manages governance, such as fine-grained access to resources. For example, if a contractor, vendor, or external user logs in via Okta, Pathlock determines whether that user is allowed to run specific t-codes in SAP S/4HANA.
Preparing for the Post-IDM Future
Transitioning away from SAP Identity Management will change how enterprises manage their digital SAP identities in the future, as SAP does not provide a direct replacement. The 2027 mainstream maintenance and extended maintenance ending in the 2030 window are creating urgency and offering a strategic opportunity for businesses to avoid a last-minute rush to modernize their identity governance approaches. As a typical SAP IDM migration takes 18 to 36 months, it still allows them to adopt a phased approach with minimal business disruption, enabling them to move to cloud-native identity management and governance solutions for future-proofing.
While SAP IDM is highly flexible, it relies heavily on custom scripts, making upgrades and maintenance difficult. Organizations should move from custom scripts to policy-driven governance, such as leveraging Attribute-Based Access Control (ABAC) or Business Rules, rather than writing scripts to determine access. Post-SAP IDM, the market favors converged governance platforms that merge traditional IGA with deep GRC, rather than using one tool for identity management and another for GRC. Pathlock Cloud handles both as a converged governance platform. Pathlock provides cross-app visibility and governance across SAP, Workday, Salesforce, and Oracle.
When evaluating SAP IDM replacements, organizations should prioritize solutions that address the four primary pillars of identity management and governance: provisioning, risk management, compliance, and audit readiness.
- For provisioning, look for automated joiner-mover-leave workflows driven by HR events.
- For risk, look for real-time, AI-driven segregation of duties and access analysis.
- For compliance, look for automated user access reviews and certifications.
- For audit readiness, look for centralized continuous monitoring and evidence-based reporting to support internal audits and compliance with regulations.