Every spring, manufacturing organizations scale up fast with additional temporary workers, contractors, and third-party specialists, each needing system access, often within hours. At the same time, many of these organizations are mid-way through digital transformation projects that are reshaping how core business functions operate.
The timing creates a compounding problem. The people and processes needed to manage access governance and security risks are already stretched, yet the volume and complexity of access requests is at its peak.
This research examines how well-equipped manufacturing organizations are to handle this pressure and whether their current access practices hold up when seasonal and structural risks collide. To find out, we surveyed 130 manufacturing technology leaders.
How Ready Are Manufacturers to Maintain Access Resilience During Seasonal Peaks?
Provisioning at Speed
Automated access provisioning and de-provisioning are foundational controls for manufacturing organizations given the sector’s high velocity and strong seasonality. During peak periods like spring, internal teams, temporary workers, and system integrators are granted access – often privileged access – as organizations rapidly onboard additional personnel. When seasonal demand subsides, that access must be revoked quickly and at scale.
However, our findings show that 74% of manufacturing organizations lack fully automated user provisioning and de-provisioning.
Figure 1.

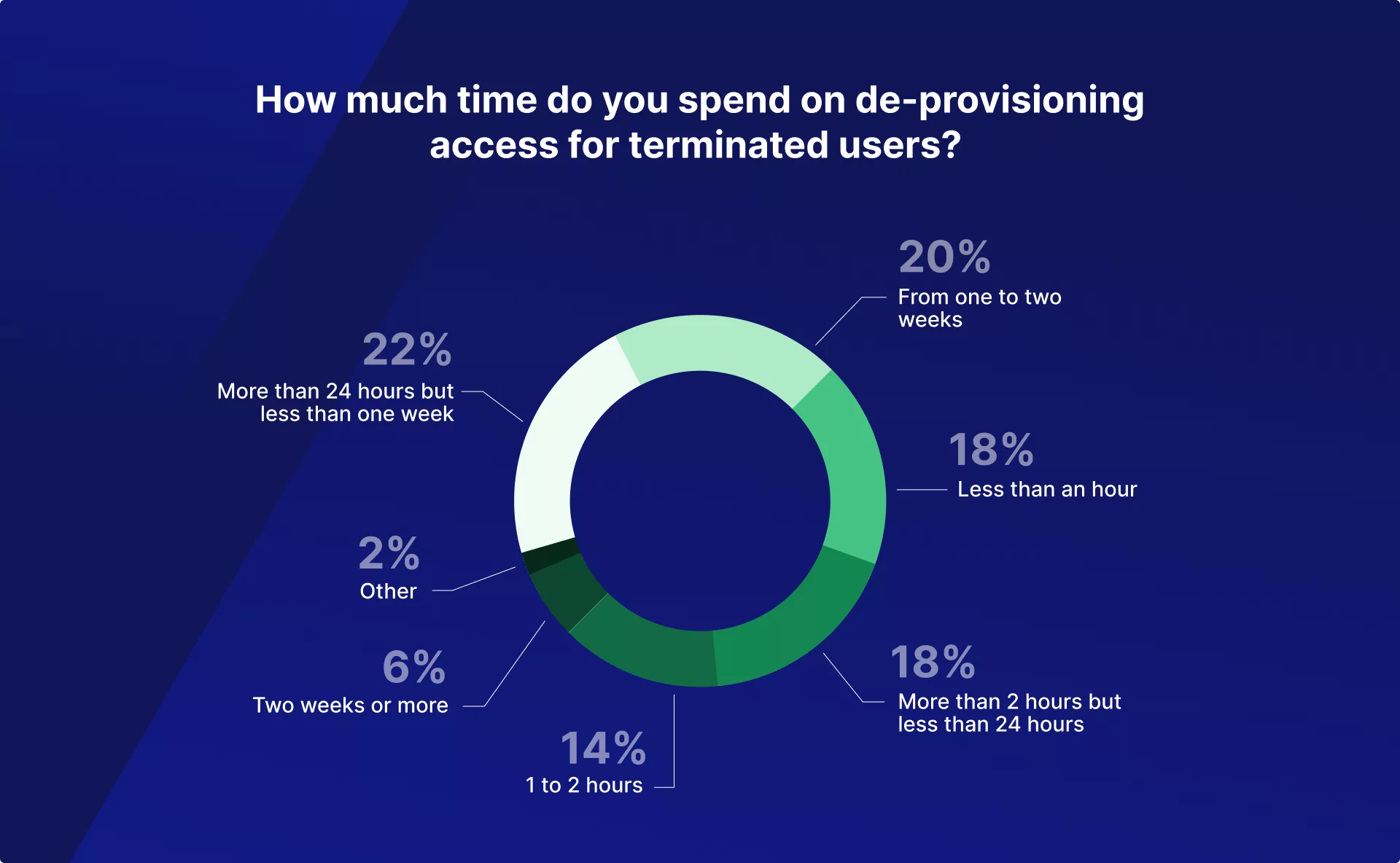
Most worryingly, 48% of manufacturing organizations fail to revoke access within 24 hours, although this timeframe is a widely accepted benchmark for effective security and governance. This delay is a significant risk multiplier.
- 48% of manufacturing organizations fail to revoke access in a timely manner
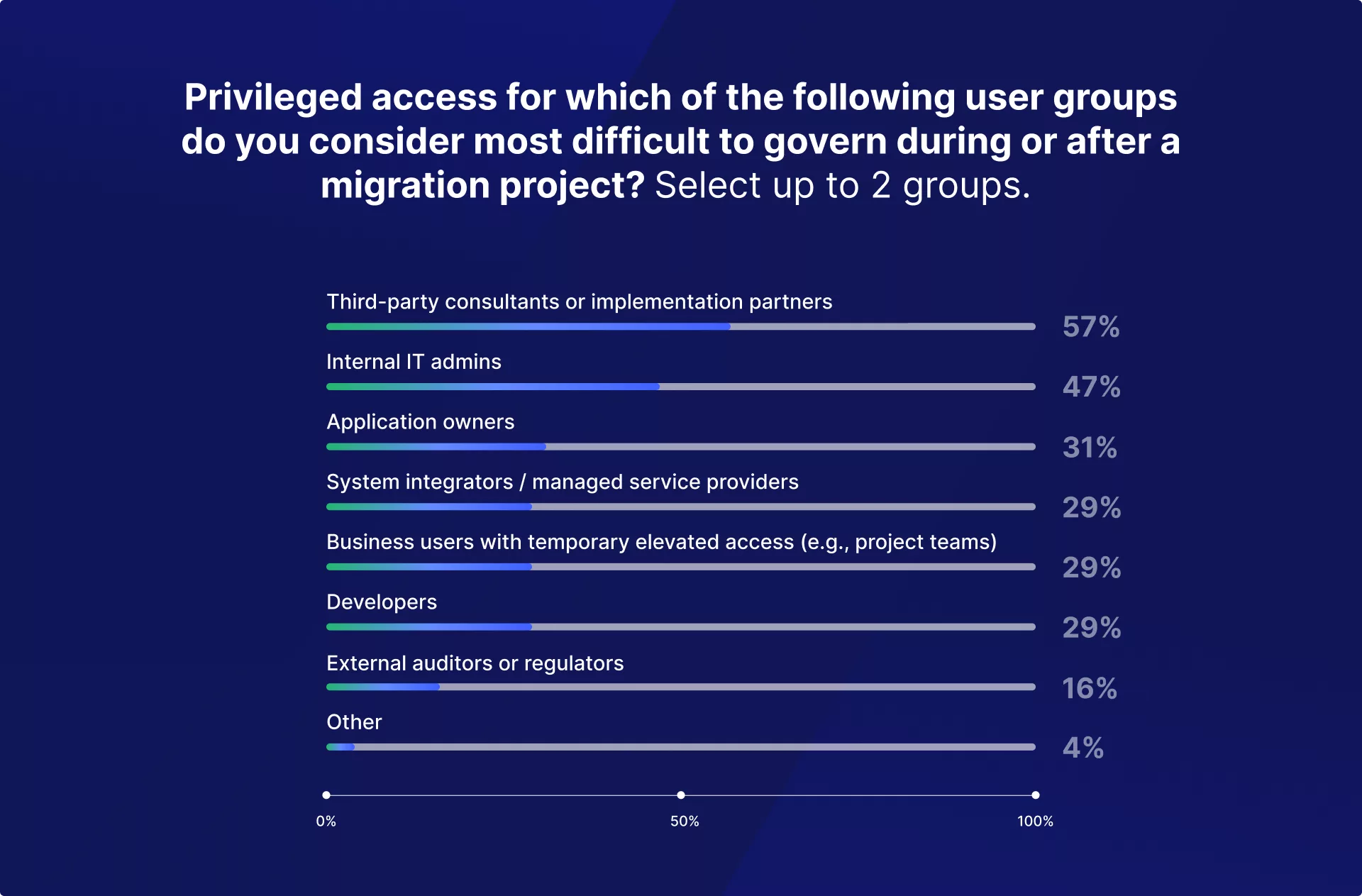
On top of that, we found that 51% don’t use automated elevated access management. And of those, 14% still operate with minimal or no governance over privileged access. Difficulty managing elevated access is concentrated among third-party consultants (57%) and internal IT administrators (47%) – precisely the user groups with the most extensive permissions.
- 51% of manufacturing organizations don’t use automated elevated access management
Figure 2.
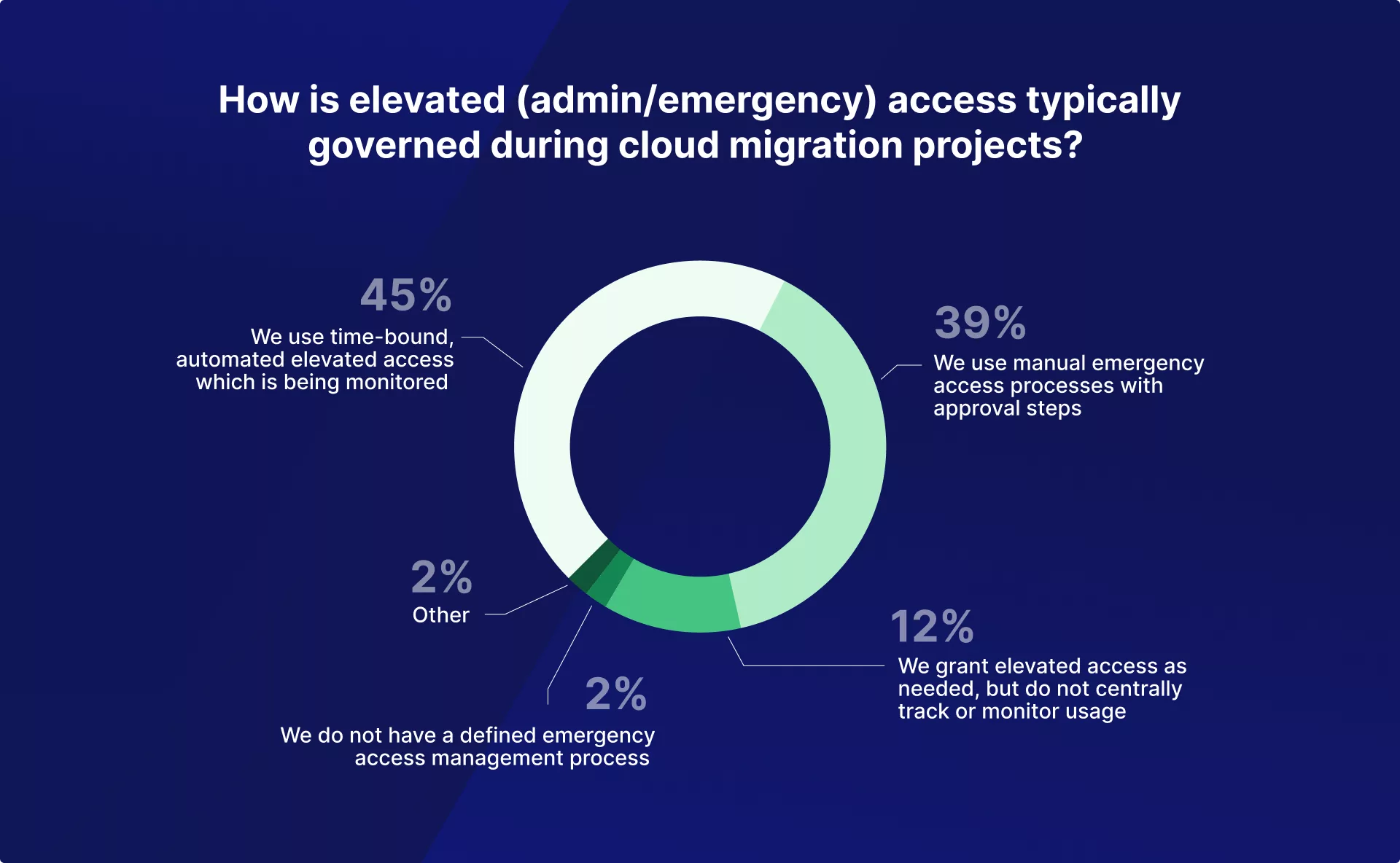
Figure 3.
Security Implications of Delayed De-Provisioning
Many high-profile breaches have occurred due to stale accounts belonging to former employees or third parties, as well as users retaining excessive privileges after role changes. In addition to these risks, dormant or “ghost” accounts with identities that remain active despite no longer being tied to a valid business need. When elevated access is not revoked in a timely manner due to a lack of automated access management, these accounts often go unmonitored and unmanaged. Such delayed de-provisioning creates additional risk as dormant accounts are prime targets for phishing, credential stuffing, password spraying, or malware-based credential harvesting. Because these accounts frequently evade regular oversight and may not trigger typical user behavior alerts, attackers can exploit them to bypass corporate defenses and operate undetected under the guise of trusted identities.
Automation Gaps Across Core Access Controls
Additionally, we explored another two key pillars in access governance – automated user access reviews (UARs) and access risk assessment.
Our analysis found that most organizations lack complete automation in these processes.
The area where manufacturing organizations struggle most is with automation is user access reviews (UARs), as 89% do not have this process fully automated.
Figure 4.
These reviews are periodic checks to ensure access remains appropriate. In manufacturing environments, reviews are especially difficult to execute at scale because access spans multiple plants, ERP modules, MES and OT-adjacent systems, shared service centers, and external vendors. Without automation, access reviews often become checkbox exercises that fail to detect access violations, increasing the risk that stale accounts and excessive permissions persist for long periods – until a breach or audit finding occurs.
“Manufacturing environments are characterized by complex plant integrations, heavy third-party involvement, and rapid operational changes. This sector’s specifics require modern, automated access governance. Without it, seasonal workforce surges dramatically increase security and compliance risk, especially where privileged access is involved.”
– Chris Radkowski, GRC Expert at Pathlock
How Digital Transformation Compounds Access Governance Challenges
In parallel with seasonal workforce cycles, manufacturing organizations are undertaking large-scale digital transformation initiatives – migrating mission-critical processes across finance, procurement, HR, and operations, to the cloud. Such a large change involves fundamental role and access redesign. When governance doesn’t keep up with this transition, risk increases tremendously. For example, legacy roles can be copied into new environments, excessive permissions can pop up, and segregation-of-duties (SoD) conflicts can be introduced unintentionally. Compounded by seasonal hiring to scale, this becomes a perfect storm for breaches.
Unfortunately, our research shows that governance controls frequently lag behind business change. Only 9% of manufacturing organizations updated their GRC controls before migration, while roughly half did so during the project phase or after go-live. Alarmingly, 14% did not update GRC controls at all.
Additionally, 61% of organizations did not conduct comprehensive SoD risk simulations before deploying new roles. This is especially problematic in manufacturing, where role complexity spans plants, shared services, procurement, maintenance, and production planning. If SoD simulations were performed partially — or skipped — excessive access enters production quietly and often goes undetected for long.
Figure 5.

Figure 6.

Why Access Governance Gaps Are Already Costing Manufacturers
The governance gaps identified in this research are already leading to real business damage. Our findings show that one in four manufacturing organizations experienced compliance violations, and one in five suffered security incidents.
- 1 in 4 manufacturing organizations experienced compliance violations
- 1 in 5 manufacturing organizations suffered security incidents
And astonishingly, 46% of reported incidents were suspected or confirmed to be linked to GRC gaps created during digital transformation.
46% of reported incidents were tied to GRC gaps created during digital transformation
Insider involvement was reported by only 22% of organizations, pointing to structural governance inconsistencies rather than isolated malicious behavior.
Figure 7.

Figure 8.

Digital transformation doesn’t create risk by itself. The risk emerges when temporary access granted during long-running transformation projects isn’t revoked at scale as workforce levels fluctuate. In manufacturing, seasonal hiring cycles turn such temporary access decisions into long-lasting exposures.
– Chris Radkowski, GRC Expert at Pathlock
Security Implications of Governance Gaps
Nearly half (46%) of reported security incidents experienced by manufacturing organizations were suspected or confirmed to be linked to GRC gaps created during digital transformation. This finding confirms that access governance goes well beyond compliance, as it is a key security and business continuity–critical domain.
In manufacturing, where seasonal workforce expansion intersects with long-term migration projects and heavy reliance on third-party consultants, identity becomes the new perimeter. Without automated provisioning, automated elevated access management, and comprehensive SoD design and simulations, organizations are not just risking audit findings — they are creating vulnerabilities inside mission-critical systems.
Recommendations for Manufacturing Organizations
The research findings revealed that access governance failures in the manufacturing sector present a systemic vulnerability that manufacturing organizations must address.
And while developing a comprehensive access governance program is a multi-stage undertaking that is individual to each organization, here are top three priorities that we recommend focusing on:
1. Enforce automated provisioning and de-provisioning as a non-negotiable control.
In a sector defined by complex environments, third-party reliance, and seasonal scale, manual and even partly automated provisioning/de-provisioning is unrealistic. These processes should be fully automated to ensure access is revoked within hours, not days, when roles change or projects end.
2. Standardize and automate privileged access for third parties and admins.
With third-party consultants and internal IT admins representing the hardest roles to manage access risks, elevated access must be time-bound, centrally monitored, and automated.
3. Embed access governance into transformation from day one.
Access governance should be treated as a core operational requirement, not a post-migration clean-up task. That means running comprehensive SoD simulations before go-live, automating user access reviews across plants and systems, and aligning governance milestones with digital transformation timelines so they don’t lead to gaps that backfire during seasonal ramp-ups.
Methodology
The research is based on data from the 2025 Digital Transformation & Access Risk Report, which surveyed IT, compliance, and security decision-makers from organizations actively undergoing cloud migration in the industrial and manufacturing sector.

