Why Organizations are Evaluating SAP Identity Management Alternatives?
SAP IDM Sunset Timeline & Strategic Implications
SAP’s decision to sunset its on-premises Identity Management (IDM) solution was part of a broader strategy to shift towards its cloud-native ecosystems, forcing organizations to reassess their identity management model to either adopt SAP’s cloud services or move to other modern alternatives. Organizations must go through critical milestones to avoid security risks, operational disruptions, and compliance gaps.
End of mainstream maintenance (2027)
SAP has announced the end of mainstream maintenance for SAP Identity Management 8.0, scheduled for 31st December 2027, which implies that no standard support, including security patches or regular updates, will be provided after this date.
Extended support period (until 2030)
SAP has also offered an extended support period until the end of 2030 for organizations that cannot fully migrate by the end of mainstream support, at an additional fee. It is not a long-term strategy but a safety net; critical fixes will be provided, but no innovations will be offered, making it a costly way to manage technical debt.
Multi-year implementation timelines for replacements
Replacing an IAM or IGA platform is not a quick project; industry experts estimate that these migrations are complex, and a full replacement for an enterprise-level environment will take 18 to 36 months. It serves as a multi-year implementation timeline that includes process redesign, discovery, solution selection, and staged migration.
Urgency for early planning and roadmap development
SAP announced this decision at the start of 2024, which, according to experts, gave organizations enough time to plan, develop roadmaps, redesign, and implement. Organizations starting after 2025 may have risked resource bottlenecks as demand for IAM consultations and implementation costs has skyrocketed; early planning would have allowed them a long implementation lead time rather than rushing and carrying over technical debt.
Key Drivers for Considering Alternatives
Organizations are using the end of support for SAP IDM to modernize their security posture and operational efficiency by migrating to other IAM platforms, such as Microsoft Entra ID or Pathlock Cloud.
They are considering the following key drivers when looking for alternatives to SAP IDM.
Cloud-first transformation
SAP is also encouraging its customers to transform their strategy to cloud-first environments, such as SAP’s own SAP Business Technology Platform (BTP) and its cloud-centric services such as CIS. Organizations can completely move away from on-premises solutions by reducing data center footprints and embracing SaaS-based services. These solutions offer higher scalability, automatic updates, and enhanced integration with other cloud platforms.
Cost optimization (CapEx to OpEx shift)
Instead of maintaining on-premises servers, databases, and the heavy upfront investment required by the Capital Expenditure (CapEx) model, organizations can transition to cloud-based Identity Governance and Administration platforms that operate on the Operational Expenditure (OpEx) model, offering predictable, scalable, subscription-based services that reduce total cost of ownership.
Reducing customization complexity
Though SAP IDM offers extensive customization options with JavaScript and SQL to implement complex business logic, it is often difficult to maintain and upgrade. Organizations are transitioning to modern alternatives with a clean-core approach that offers no-code/low-code configurations, reducing customization complexity, simplifying maintenance, and enabling more resilient upgrades.
Expanding beyond SAP-centric environments
While SAP IDM offered more integration with SAP landscapes, it struggled to integrate with non-SAP applications and cloud environments such as AWS, Google Cloud, and Azure. Organizations are seeking expansion beyond SAP-centric environments, looking for solutions that provide identity and governance lifecycle management with a single pane of glass across the entire enterprise.
Improved user experience & modern architecture
Organizations are looking for improved user experience and modern architecture. Modern IGA tools offer user-friendly and mobile-friendly self-service portals with access request and approval features, mostly leveraging API-first design and services and supporting modern authentication and federation standards like SAML 2.0, OIDC, and SCIM. This enables organizations to integrate quickly with SAP and non-SAP HR systems, such as SAP SuccessFactors and Workday.
How are SAP Alternatives selected and evaluated?
Evaluation and selection of an alternative to replace SAP IDM is a complex process that requires balancing technical requirements and future scalability, from defining requirements, shortlisting solutions, and conducting proofs of concept (POCs). Organizations use a scoring model based on several core categories and features for their SAP and non-SAP landscapes.
Core Evaluation Categories
Organizations typically follow the scores and feedback from major market analysts such as Gartner, PeerSpot, and KuppingerCole for IAM and IGA vendors. These scores are based on distinct categories.
Evaluation and contracting
This includes assessing the vendor’s financial stability, market position, and the flexibility of their Service Level Agreements, based on customer ratings and peer reviews.
Integration and deployment
The focus here is to look for time-to-value, availability of out-of-the-box connectors for SAP systems such as SAP S/4HANA, SAP BTP, and SuccessFactors, non-SAP integrations, and hybrid deployments.
Service and Support
Organizations assess vendors’ global support footprint, specifically 24/7 support, comprehensive documentation, training, and certified implementation partners such as PwC, Accenture, or Deloitte, who understand legacy SAP IDM and new cloud-based services, as well as vendors’ integration capabilities.
Product capabilities
Organizations look for IGA and IAM features, such as identity lifecycle management, self-service, automated provisioning, access requests and approvals, certifications, security, and authentication, including SSO, MFA, adaptive authentication, and analytics services.
Pricing and total cost of ownership (TCO)
Organizations look at the total cost of ownership, including implementation costs, long-term cost management, and training beyond the initial solution licensing, and compare it with their legacy on-premises maintenance costs.
Key Organizational Considerations
As the identity requirements of each organization differ, the following organizational factors contribute to the evaluation and prioritization of alternatives.
Size and complexity of the SAP environment
The size and complexity of the SAP environment matter most; large enterprises spanning globally, with 50+ SAP instances across multiple regions and production lines, have different needs than a small organization with five or fewer SAP instances. Some solutions may be suitable for small organizations, while others are suitable for large enterprises.
Degree of IDM customization
As large organizations rely on extensive SAP IDM customization using JavaScript and SQL, they must decide whether to go with a clean core or seek a solution expert to migrate complex custom logic.
Hybrid vs. cloud-first strategy
It depends on the organization’s existing strategy. If they want to move towards SAP S/4HANA cloud, they may prefer tools like Entra ID or Saviynt for SAP and non-SAP integration. In contrast, organizations with legacy SAP ECC systems may prefer a hybrid-capable solution.
Regulatory and audit requirements
Industry-specific organizations, such as Healthcare and Finance, are subject to strict HIPAA, GDPR, and SOX compliance requirements. They will prioritize built-in audit-ready reports and dashboards, along with risk analytics, SoD, and certifications.
Budget allocation
SAP IDM is a perpetual licensing tool with a CapEx model. Transitioning to a subscription-based OpEx model will require a shift in how budgets are distributed and managed for IT teams.
Internal IAM expertise
Organizations with internal SAP-specific expertise may seek a solution with the same logic and flow so that the same skills can be applied to a new solution, or a new solution should offer extensive training paths.
Core SAP IDM Capability Mapping
Organizations also perform gap analyses and may map new tools’ features against SAP IDM features.
Handling 50+ SAP systems
An alternative solution should demonstrate high concurrent provisioning across multiple SAP systems and the ability to manage high user volumes without degrading performance.
Custom scripting & advanced logic
Organizations evaluate alternatives for managing complex scripting and advanced logic, such as attribute transformation with JavaScript or no-code workflows.
Segregation of Duties (SoD)
Segregation of Duties is a critical requirement for organizations. The ability to perform cross-application SoD checks, such as preventing users from creating a vendor or approving a payment.
License management
Ability to offer license management, e.g., identifying inactive users or over-licensed users in different SAP or non-SAP systems.
Multi-system orchestration
Ability to provide multi-system orchestration, such as user and access provisioning simultaneously in SAP, Active Directory, ServiceNow, and Salesforce.
Risk analysis & Governance
Ability to provide preventive risk and governance analysis using artificial intelligence and machine learning for identification of high-risk access patterns upon provisioning, instead of finding them during periodic audits.
Leading SAP Identity Management Alternatives
The SAP identity management alternatives market is dominated by a few key players, ranging from cloud-native IDaaS (Identity as a Service) providers to Governance, Risk, and Compliance (GRC) solutions.
Best SAP IDM alternatives include:
Microsoft Entra ID
Microsoft has evolved as a primary alternative to SAP IDM, due to its strategic partnership with SAP, and most organizations already own it as Microsoft 365. Microsoft Entra ID offers robust identity governance features, designed for integration with SAP S/4HANA, SAP SuccessFactors, and SAP BTP. Its strength lies in seamless integration with the M365 ecosystem and identity governance modules, which manage lifecycle management and access reviews. It is best for organizations seeking a cloud-first model and a heavy investment in the Microsoft ecosystem.
Pathlock Cloud
Pathlock Cloud is mainly a GRC provider. It combines IGA with fine-grained Access Control and GRC capabilities. Its key strength is to look inside SAP applications to track transaction-level risks and provide granular Segregation of Duties. It is the best fit for organizations with high compliance requirements under SOX and GDPR and deep visibility into SAP transaction codes and authorization objects.
Pathlock Cloud: In-Depth Analysis of Leading SAP IDM Alternative
The Identity Governance and Administration market is vast; some vendors focus on deep SAP integration, while others emphasize broader enterprise-level capabilities, such as platforms like Active Directory and ServiceNow.
Pathlock is a cloud-based identity governance and access management solution. It has positioned itself as a premier SAP IDM alternative for organizations looking for identity management through the lens of Governance, Risk, and Compliance. Pathlock Cloud is a converged IGA solution with Application Access Governance, designed to offer a single pane of glass for identity management across multiple ERP landscapes. It has a strong focus on SAP security, risk management, and compliance, not just managing who has access to what, but also deep integration that actually looks for transactional-level activities. It has deep enterprise-wide support for SAP-centric systems and also provides 100-plus integrations with other enterprise applications, including Workday, Oracle, Salesforce, and NetSuite. Pathlock has a longstanding presence in SAP access governance and control environments.
Architecture & Deployment Model
Pathlock Cloud is designed as a cloud-first architecture, reducing the need for on-premises infrastructure and its maintenance. It supports hybrid SAP landscapes and reduces the gap between SAP ECC and Cloud-based SAP S/4HANA or BTP. Pathlock Cloud integrates with ERP, HR, and financial systems, acting as an orchestrator between them and, as a source of truth, integrating with downstream systems, such as SAP SuccessFactors or Workday. Pathlock Cloud is designed for continuous compliance monitoring, rather than traditional IGA solutions that perform periodic audits, such as quarterly or annual.
Core Capabilities
Core capabilities of Pathlock Cloud include:
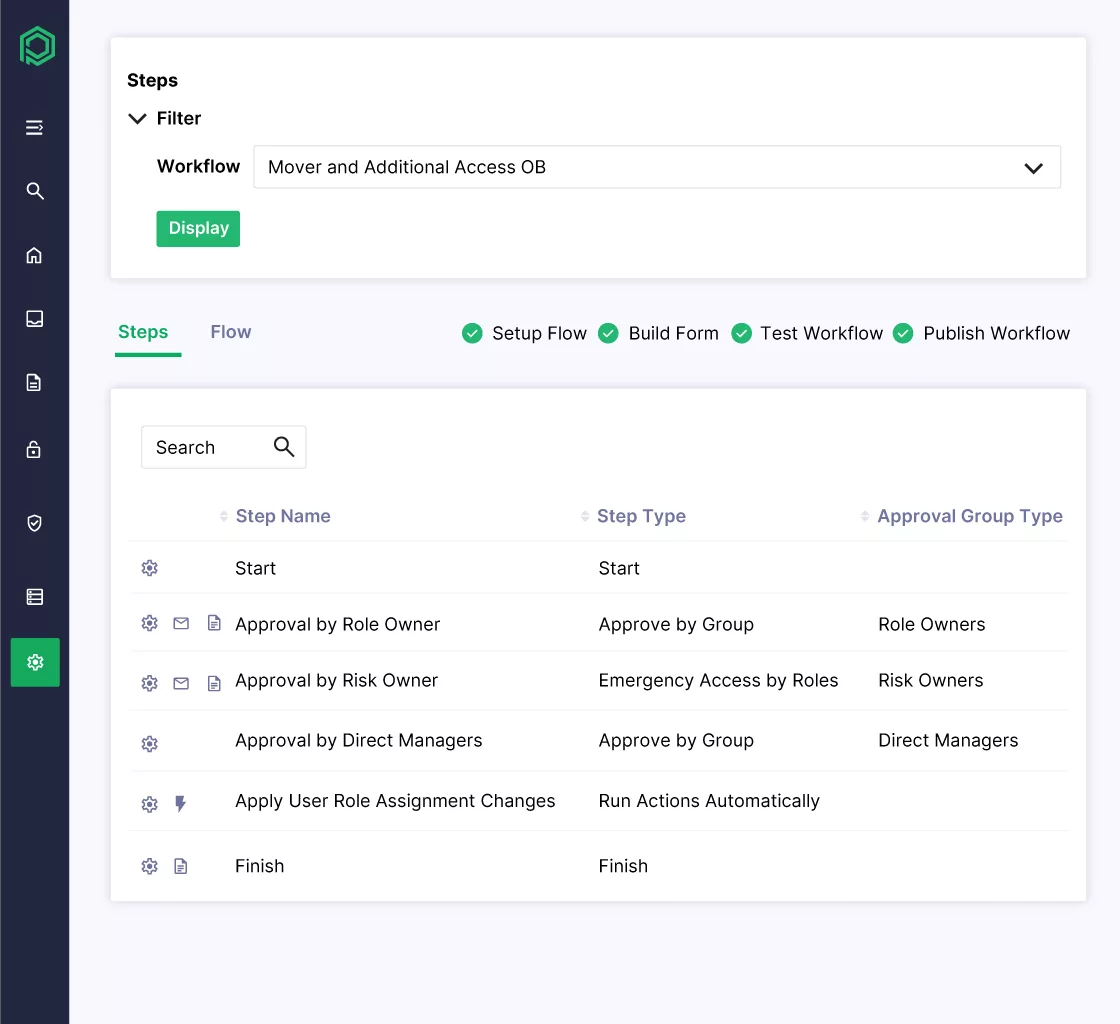
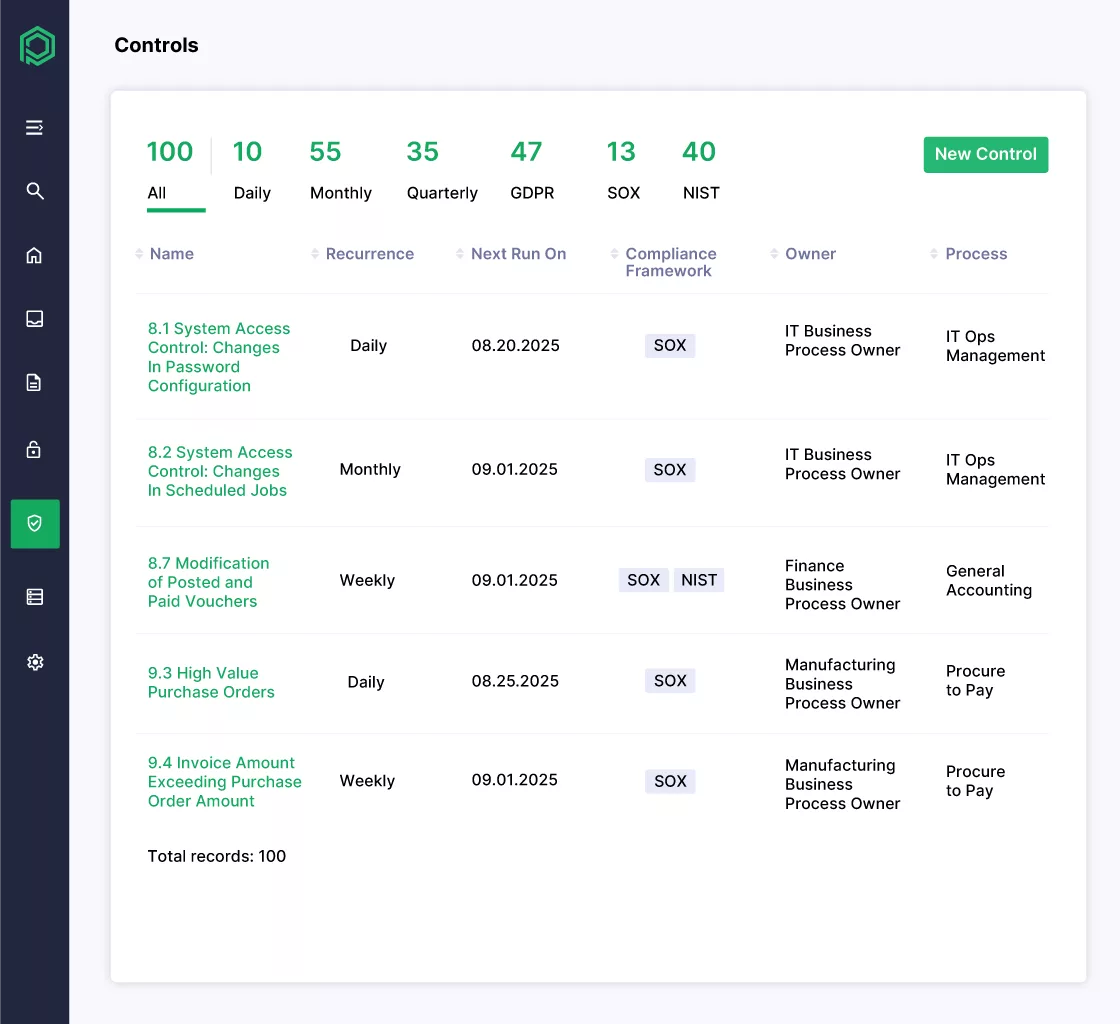
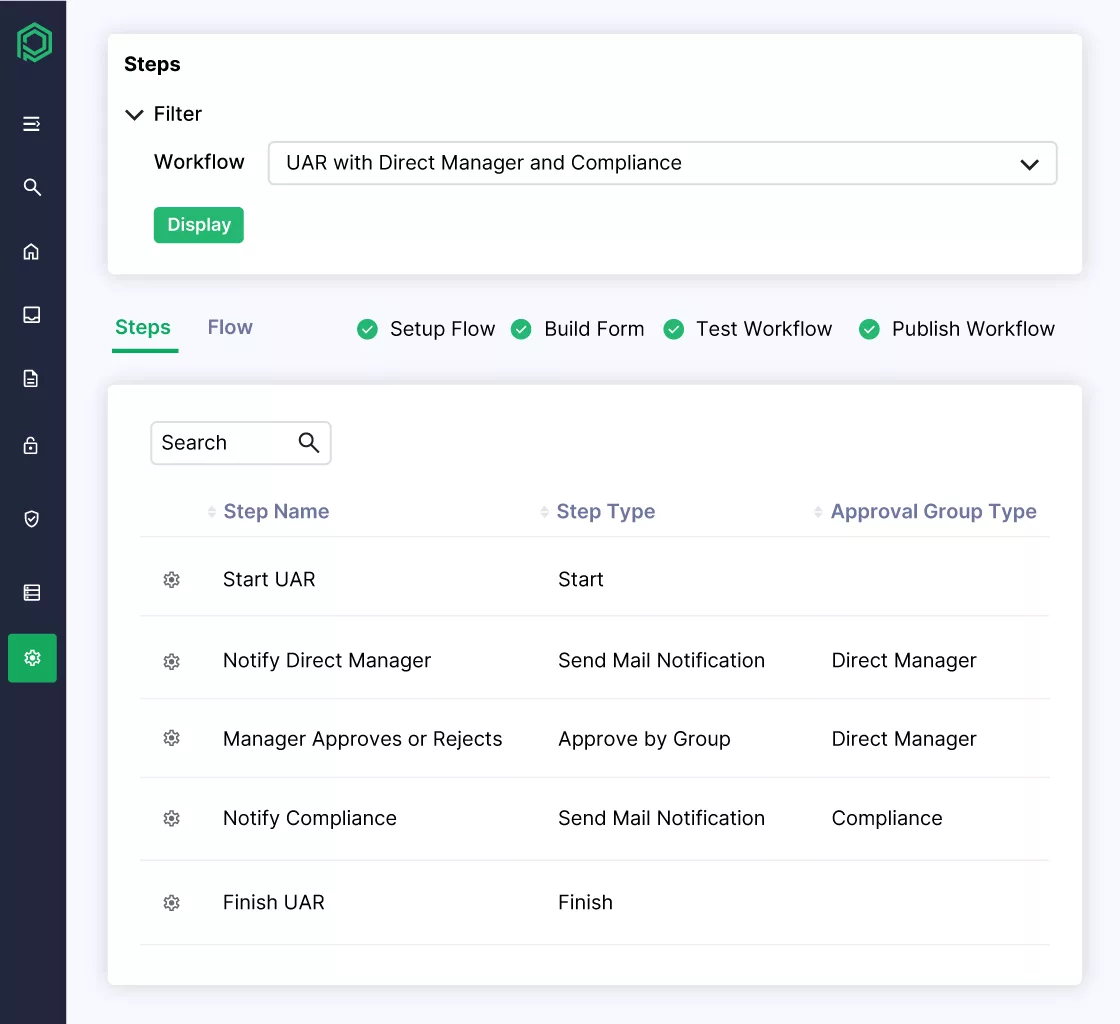
- Access governance & lifecycle management, such as automated Joiner-Mover-Leaver processes along with access request and approval workflows.
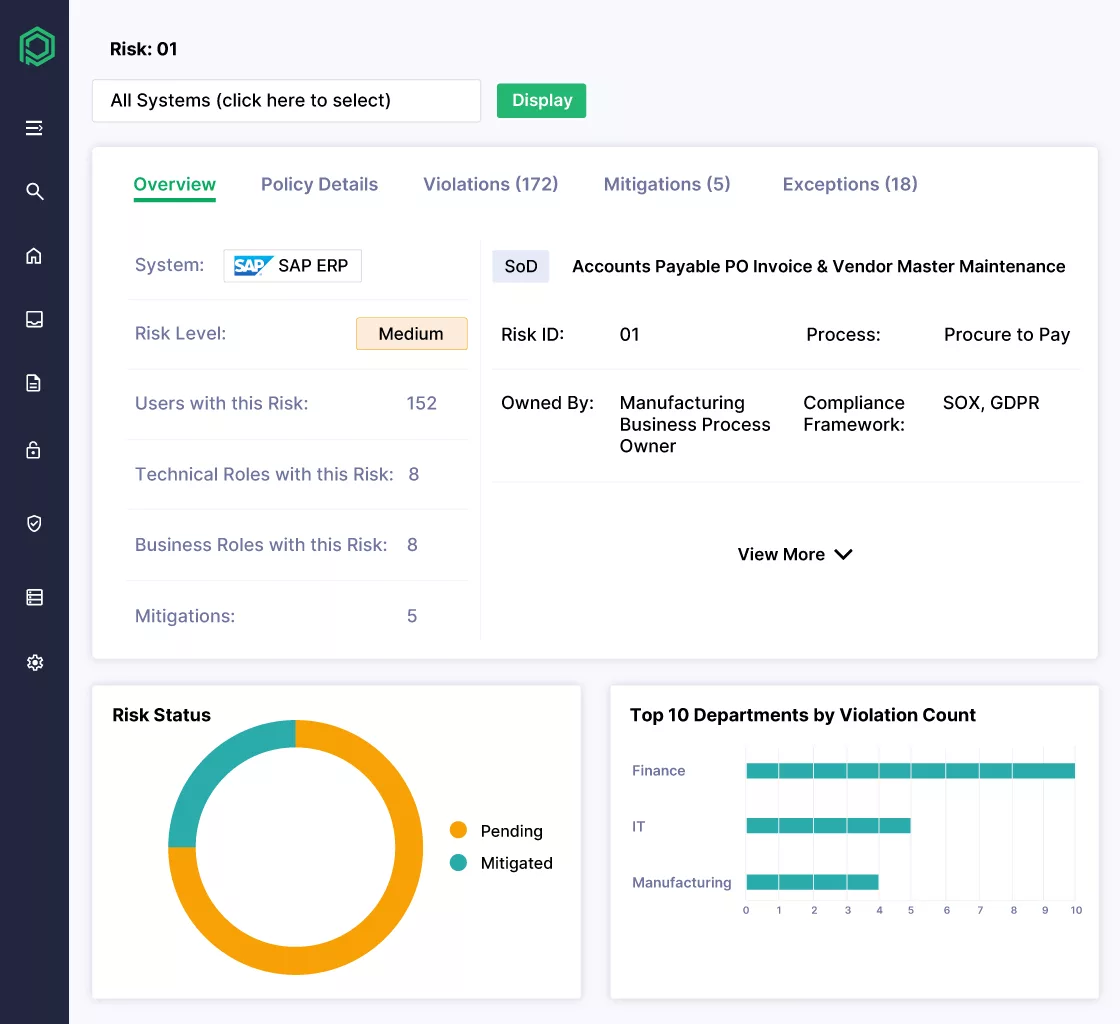
- Segregation of Duties (SoD) analysis and remediation, e.g., identifying transactional code and authorization object level conflicts across different systems, e.g., SAP and Salesforce.
- Role design, mining, and optimization, enabling organizations to clean up their overprovisioned roles before migrating.
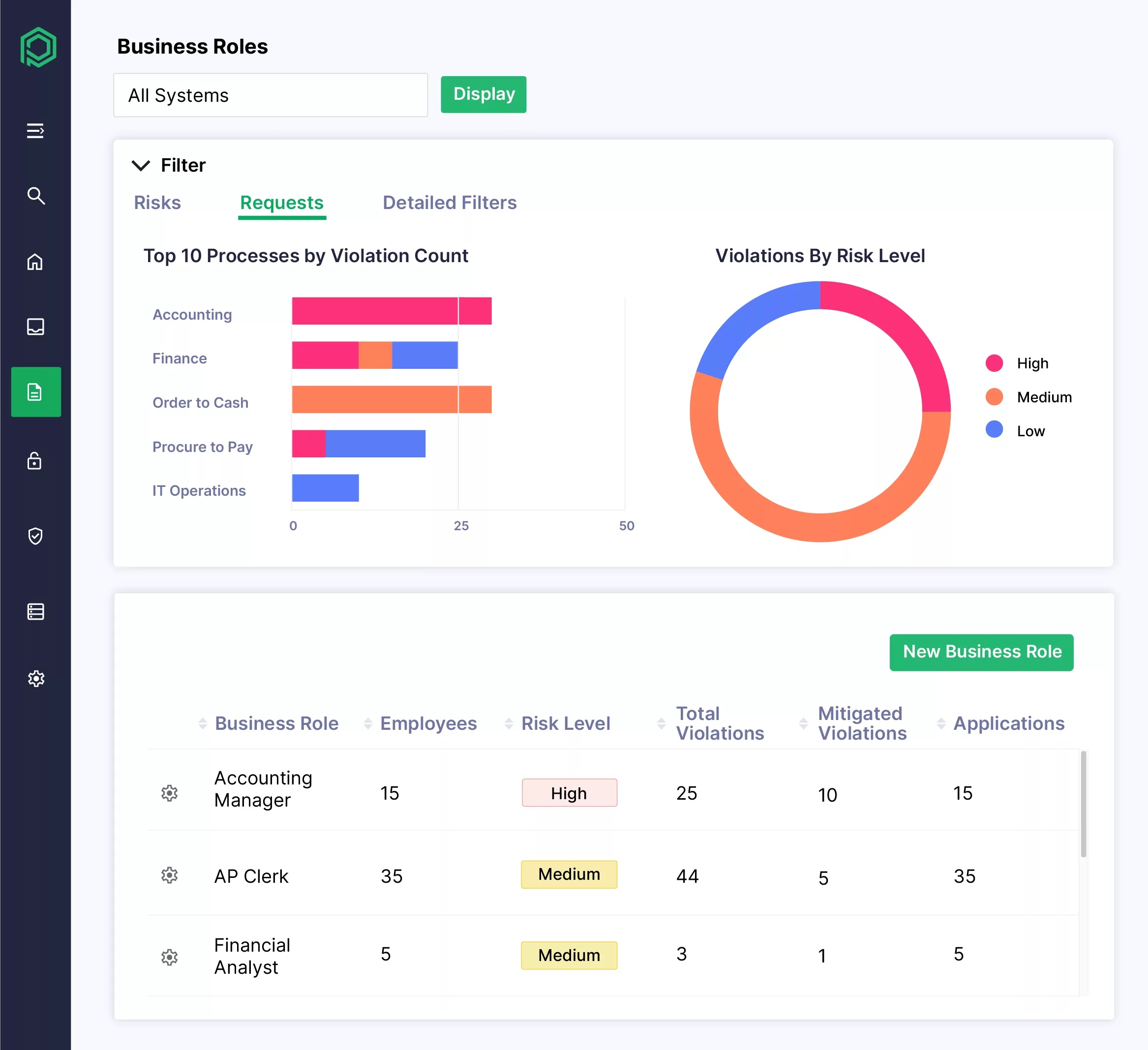
- Risk-based access controls such as risk scoring and access assignments, policy enforcement, and automated remediation workflows.
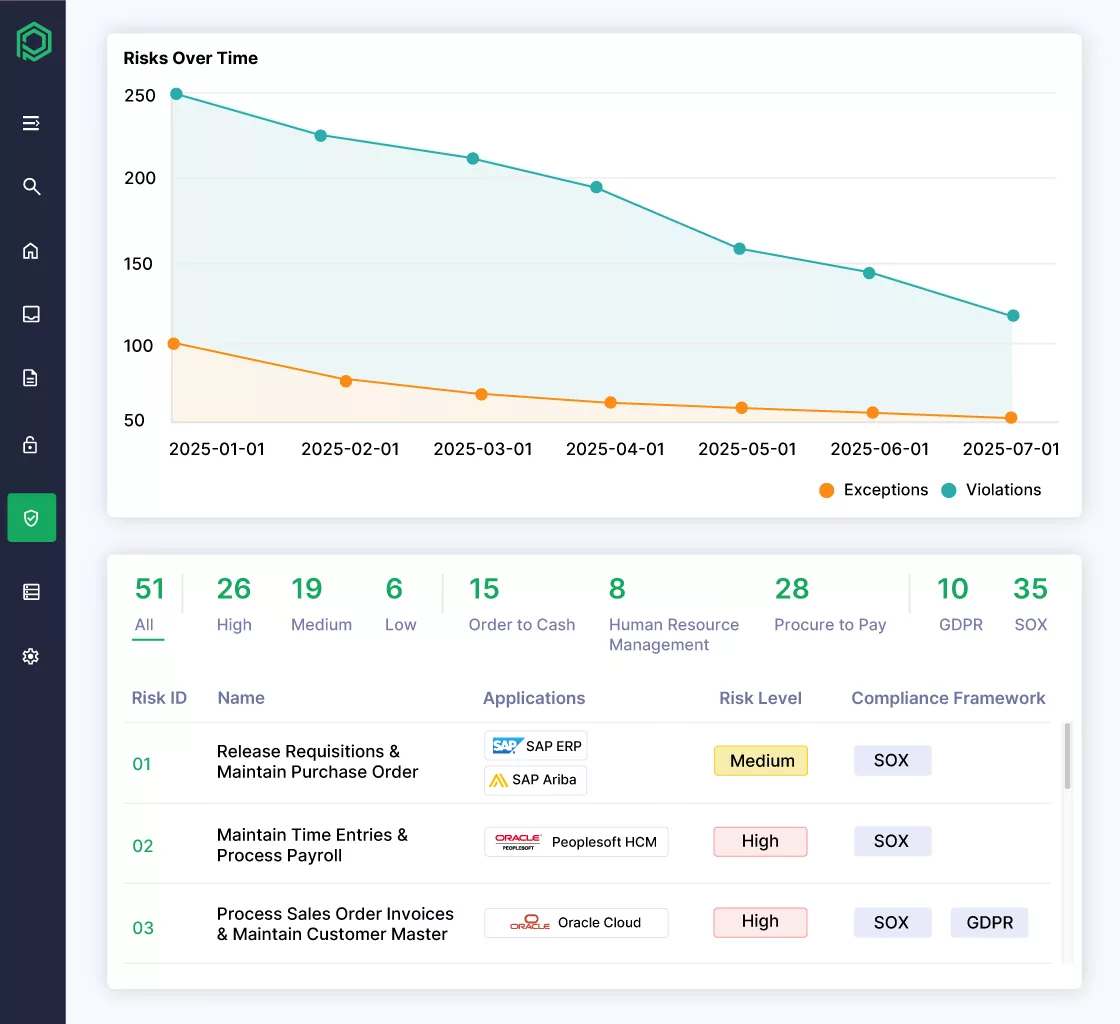
- Continuous control monitoring with 100% transaction monitoring in real-time to identify policy violations as they occur, unlike traditional periodic reviews, detective, and preventive controls, along with policy violation alerts.
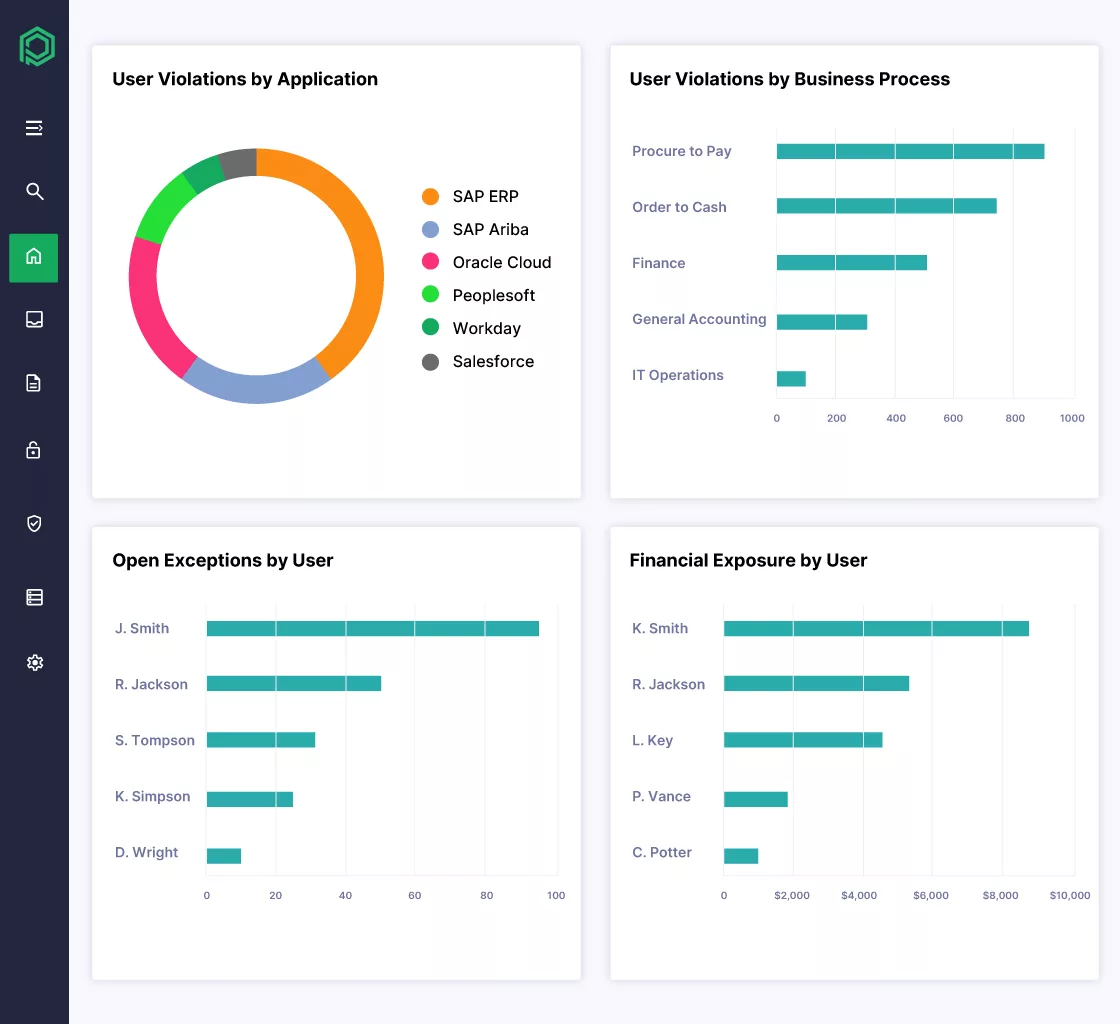
- Audit-ready reporting with out-of-the-box customized reports for regulations like GDPR and SOX for internal audit requirements, built-in compliance dashboards, and evidence collection for internal and external audits.
- Emergency access management capabilities for elevated access with time-bound access and full session monitoring and logging.
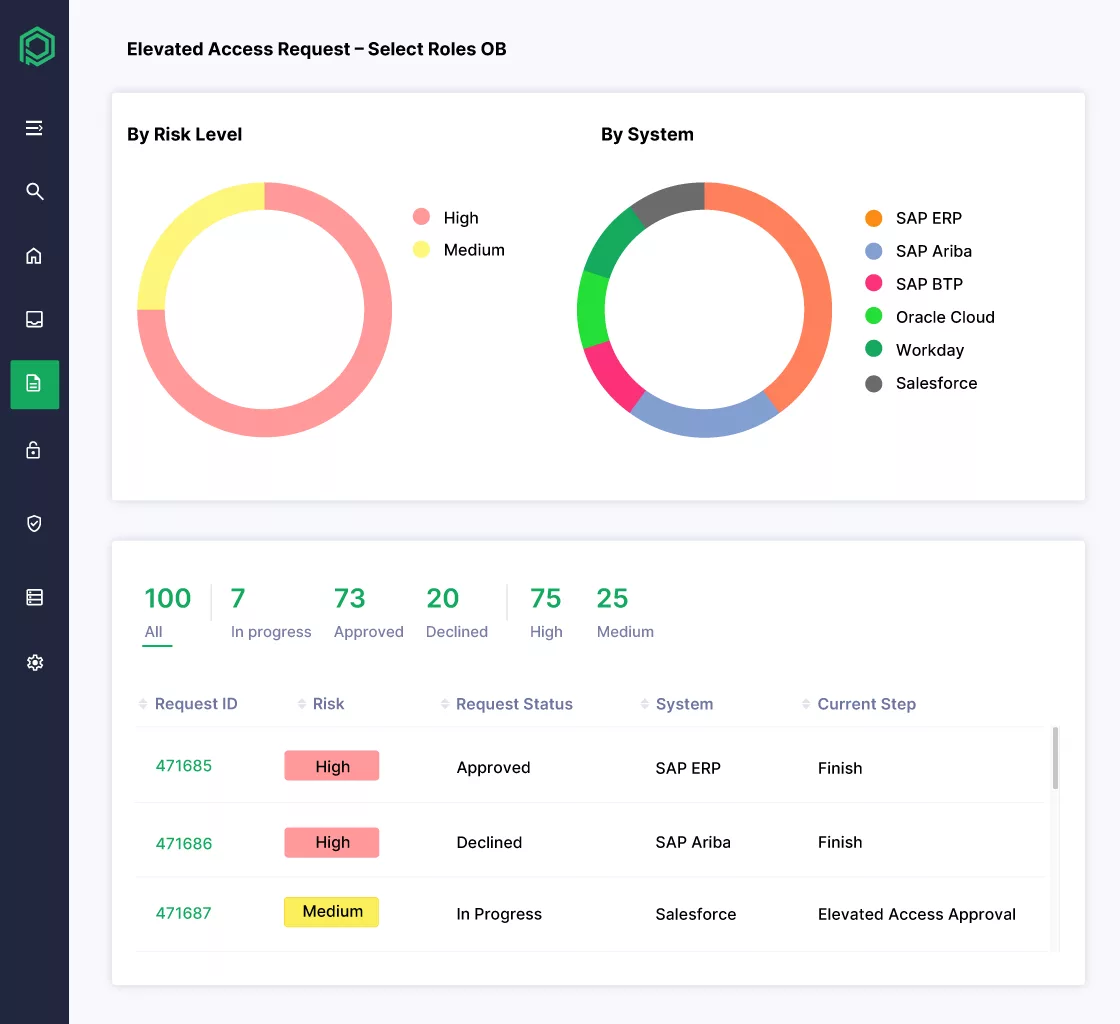
- Workflow-based multi-step access approvals, policy-based routing with full audit trail and documentation.
SAP-Specific Strengths
Pathlock Cloud offers a deep understanding of SAP authorization concepts, roles, and profiles that align with SAP’s security model, which other generic IGA tools often miss. It provides embedded SAP risk analysis and pre-configured SoD rule sets for SAP modules, which provide continuous risk assessment within SAP systems. Pathlock Cloud is designed to support SAP ECC and S/4HANA on-premises and SAP cloud applications, and to align strongly with SAP GRC replacement strategies. Pathlock Cloud focuses on SAP license optimization and access transparency by analyzing actual user activity, identifying duplicate, dormant, and misclassified users, and then suggesting appropriate SAP licenses.
SAP IDM and Pathlock Capability Mapping
| SAP IDM capability | How Pathlock replaces and improves it |
|---|---|
| Provisioning fulfillment (SAP roles & accounts) | Automated provisioning with risk-aware request checks and attribute-driven approvals; full audit trail. |
| Joiner/Mover/Leaver workflows | Configurable JML workflows with standardized patterns that reduce custom scripting and technical debt. |
| Self-service access request portal | Modern self-service requests with policy-based routing, SoD prevention, and business-context visibility. |
| Role / access management | Role design and access governance with SAP-native entitlement depth (transactions/authorization objects). |
| Certifications / user access reviews | Risk-prioritized certifications with contextual data (risk + business context) to drive least privilege. |
| Integration hub (SAP + other apps) | Unified governance across SAP and non-SAP applications with consistent policies and reporting. |
| Audit support | Regulatory-ready reporting plus continuous monitoring and centralized evidence collection. |
Advantages
- Pathlock Cloud is designed for audit committees as much as it is designed for IT departments, with strong compliance-driven governance capabilities, supporting several regulations like SOX and GDPR.
- Pathlock is recognized for its direct customer engagement model and support reputation.
- Pathlock Cloud has operated in SAP security and governance for many years, proving itself as a specialist rather than only a broad IAM vendor.
- Pathlock Cloud is purpose-built for SAP-heavy organizations, avoiding the generic feel of other IGA tools by understanding SAP’s architecture and rule sets for optimization.
- Pathlock Cloud emphasizes reducing audit findings by automating SoD checks before granting access, enabling organizations with proactive risk prevention rather than reactive audit remediation.
Limitations
While Pathlock Cloud supports other enterprise apps, its focus is more on SAP systems than broad enterprise IAM competitors such as Microsoft Entra or SailPoint. Organizations without an ERP footprint may find SAP too specialized. Organizations looking for advanced Customer IAM (CIAM) or unstructured data governance may need complementary solutions for full IAM coverage, or Pathlock Cloud can integrate with other tools to provide that coverage. Pathlock Cloud’s depth of SAP specialization is considered to exceed that of small or non-SAP-centric organizations.
Pricing Considerations
Pathlock Cloud is positioned as a governance-focused solution; its pricing is typically subscription-based on the number of users and connected applications. Pathlock Cloud cost is typically aligned with compliance-driven enterprises. If organizations are replacing SAP IDM and SAP GRC Access Control with Pathlock Cloud, they are consolidating multiple maintenance costs into a single subscription.
Best Fit Use Case
Pathlock Cloud is an ideal choice for organizations:
- If you run complex SAP-heavy environments such as SAP ECC, SAP S/4HANA, and SAP SuccessFactors.
- If the organization is highly regulated, e.g., subject to FDA or SOX requirements or similar regulations, where strong SoD enforcement and continuous compliance monitoring are required.
- If the organization is planning to migrate its governance capabilities from SAP IDM or SAP GRC to the cloud.
- If the organization requires audit-ready reporting and comprehensive visibility into risk management.
- If the organization prioritizes regulatory compliance and access risk mitigation.
Migration approach: Move off SAP IDM without business disruption
Replacing SAP IDM is a program, not a point project. Pathlock supports a phased approach that reduces risk while maintaining operational continuity:
- Discover and document existing IDM use cases, custom logic, integrations, and approval paths (including “hidden” workflows).
- Clean up and rationalize roles and entitlements to reduce over-provisioning before migration.
- Implement core identity lifecycle and access request workflows first, then expand to deeper governance (SoD, certifications, emergency access).
- Run in parallel where needed to validate provisioning and policy outcomes before cutover.
- Expand governance coverage across additional SAP systems and critical non-SAP applications once the core is stabilized.
SAP Cloud Identity Services & SAP Identity Access Governance (IAG)
Strategic SAP Direction
As SAP moves away from its on-premises Identity Management solution, there is no single product to replace it; it provides identity management and access governance through SAP Cloud Identity Services and SAP Identity Access Governance (IAG). SAP Cloud Identity Services include many services, such as Identity Authentication (IAS), which manages SSO and MFA, and Identity Provisioning (IPS), which manages user data flow and automates the lifecycle between SAP applications, such as SuccessFactors and S/4HANA. SAP uses its Identity Access Governance (IAG) service as a replacement for the SAP IDM governance layer, which provides access requests, Segregation of Duties for risk analysis, and access certifications for compliance.
Strengths
SAP’s strength lies in:
- Its native SAP integration, which offers Zero Trust support, the most seamless integration with SuccessFactors, Ariba, and S/4HANA, and an understanding of authorization objects and role collections better than any other third-party solution.
- SAP Cloud Identity Services function as a single source of truth for identity control across SAP Cloud and hybrid environments.
- Many SAP subscriptions include basic usage of IAS and IPS components within SAP licensing, reducing the additional licensing needs.
- SAP uses advanced AI-driven risk analysis in IAG, the same as it uses in SAP GRC, offering deep insight into Segregation of Duties for SAP applications.
Limitations
- While strong at the SAP native ecosystem, SAP offers limited third-party cloud integrations; it is more difficult to connect with non-SAP applications, such as Salesforce, AWS, or legacy apps, than SailPoint or Saviynt.
- It is less mature than other specialized IGA platforms, lacking some advanced features that other long-standing market leaders may provide best, such as out-of-the-box workflows and advanced role mining capabilities.
- Organizations often find SAP cloud services with reduced enterprise-wide governance scope and think they may need a broader IGA tool to manage their non-SAP landscapes.
Best Fit Use Case
- SAP IAG and Cloud Identity Services are ideal for SAP-centric enterprises, with more business-critical applications within the SAP ecosystem.
- For organizations that require moderate SAP complexity, no extreme custom scripting flexibility of their old on-premises IDM, but require robust governance.
- Suitable for SAP-centric organizations that want to strictly align with SAP’s clean core roadmap and maximize their SAP ecosystem investments, and do not want their security stack to depend on third-party vendors.
SAP Identity Management vs. Competitors: Comparative Themes
Integration Capabilities
SAP excels in SAP-native integrations; SAP GRC is specifically designed to navigate the complex ABAP and Java stacks across the SAP ecosystem and to manage concepts like structural profiles, composite roles, and SAP HR triggers. Modern IGA competitors offer broader multi-platform reach. Platforms like Pathlock offer numerous connectors for non-SAP cloud-based applications like ServiceNow and Salesforce. In contrast, SAP IDM often struggles with integrations and requires heavy custom coding to achieve them.
Customization & Flexibility
Modern SaaS identity and access management solutions, including Pathlock, shift from heavy custom coding toward a configuration-driven approach. In contrast to SAP IDM, which relies extensively on custom scripts and bespoke logic, these platforms emphasize low-code/no-code workflows, prebuilt integrations, and UI-based configuration. While this approach limits deep modifications of the underlying engine, it significantly reduces technical debt and enables more seamless upgrades, security patching, and ongoing maintenance.
Pricing & Setup Costs
The identity management financial model has shifted from capital-intensive initial investments to predictable operational expenses; SAP is often considered a higher initial investment due to perpetual licenses and hardware costs, as well as long and expensive implementation costs. Cloud-based competitors offer subscription-based pricing, a per-user/per-month model, lowering the entry barrier, but can become expensive when the user base grows, and still incur no cost for maintaining internal infrastructure.
Deployment Complexity
SAP IDM is highly customizable, but that complexity comes with the requirement to write custom scripts for every unique business process, which in turn leads to long implementation cycles. Modern competitors outperform SAP IDM on time-to-value; they deliver faster deployments with basic integrations often completed in weeks, but they also reduce control, encouraging organizations to adapt their business processes through standardization and out-of-the-box workflows.
Compliance & Audit Capabilities
SAP is still the gold standard for SAP IDM customers to adopt its Identity Access Governance (IAG) and SAP GRC as a replacement for compliance and audit capabilities, offering the most granular SoD analysis with deeper integration for transaction codes and authorization objects at the level. Modern competitors offer intelligence-based visualization for auditors based on continuous monitoring, offering advanced auditing with deep audit trails and historical reporting, making it an ideal choice for highly regulated industries.
Privileged Access Focus
While some IGA manages everyday user access, privileged-access-focused solutions manage administrative and high-risk accounts. Pathlock’s Elevated Access Management enables organizations to control, monitor, and audit privileged activities such as emergency access (e.g., Firefighter usage), sensitive transactions, and critical data access in real time. With capabilities like session monitoring, automated controls, and detailed audit trails, Pathlock helps ensure that elevated access is tightly governed, reducing risk and strengthening compliance across complex ERP environments.
SAP-Optimized Solutions
There are specific IGA vendors that built their entire value proposition on deep knowledge of complex SAP authorization architecture, such as Pathlock Cloud, which focuses on fine-grained Application Access Governance to monitor Segregation of Duties at the transaction level across SAP and other ERPs. One Identity is another SAP-certified partner with an extensive library of connectors to handle the ABAP-level nuances of SAP IDM and deliver integrations better than other generic cloud solutions.
Migration Strategy from SAP IDM
Migration from SAP Identity Management to a suitable alternative can be a multi-year journey, which requires careful planning, assessment of critical migration risks, and evaluation of business transformation strategies. It can also be a shift from a developer-centric approach to a governance-centric mindset, leaving technical debt behind and aligning with modern security and governance standards and best practices.
Planning Phases
Ensuring business continuity and intact security coverage requires a structured framework and planning. Organizations should consider the following six points when planning.
- IAM Maturity Assessment: Before selecting an IAM/IGA tool, organizations should evaluate the maturity of their existing identity processes, identification of orphan or inactive accounts, workflows, business roles, and assessment of identity data. As a best practice, organizations should document all these.
- Requirement Prioritization: Organizations should clearly prioritize their requirements before selecting an alternative tool. Not all features are treated equally; they could engage techniques like MoSCoW (Must have, Should have, Could have, and Won’t have) for requirements, e.g., SoD, automated provisioning, or self-service portal.
- Vendor Evaluation: Perform Request for Proposal (RFP) and Proof of Concept (POC) for vendor evaluation. POC should focus on critical requirements or complex use cases, such as integration with legacy SAP systems, lifecycle automation, governance, deployment models, analytics & reporting, cloud-on-prem-hybrid support, and TCO, before shortlisting.
- Implementation Roadmap: Start developing an implementation timeline with a phased approach; a big bang approach is rarely successful vs an incremental approach, such as starting with a source of truth first, like SuccessFactors or Workday, then following high-risk SAP systems, and then finally non-SAP applications.
- Migration and Transition: In this stage, perform data extraction, cleansing, and transformation, migrate roles and permissions, run the new IGA system in parallel with SAP IDM to make sure that logic is working as intended, then go for the final cutover.
- Post go-live Optimization: Once the new system is live, shift the focus to performance tuning, user feedback, refine the AI/ML-driven access analysis and recommendations, and expand the footprint to more cloud-based infrastructure gradually.
Critical Migration Risks
Organizations should manage critical migration risks proactively to avoid security gaps and project delays.
- The biggest risk is over-customization replication. Trying to make a new solution behave exactly like SAP IDM by replicating legacy custom scripts in a modern IGA tool leads to the transfer of technical debt. It reduces the chances of standardization benefits, which can lead to project failure overall.
- Understanding SAP’s complexity, such as its hierarchical role structure and complex authorization objects, requires custom or SAP-certified connectors and a well-versed team to understand the SAP basis and security model; otherwise, audit and SoD gaps will emerge.
- Many organizations would want to maintain their hybrid landscape, such as on-premises ECC and cloud S/4HANA, for years until they fully migrate to the cloud. The new migration strategy must ensure the solution can manage both systems without integration or performance degradation.
- Organizations should keep in mind the growing shortage of skillsets, such as experts and partners in both SAP IDM and modern IGA alternatives, integrations, and governance frameworks. They should secure those skill sets before the implementation stage.
Opportunity for Business Transformation
The end of SAP IDM life should be considered as a positive opportunity for business transformation rather than just a technical upgrade.
- Organizations should adopt a clean core approach for process standardization when moving away from complex code to industry-specific standards and best practices for identity lifecycle management, centralized access governance, and automation.
- Adapting advanced automated provisioning, workflows, analytics, and self-service is another expansion organization that the organization should look at as a transformation strategy, as SAP IDM lacks this functionality. Advanced automation and self-service password management reduce the burden of manual tickets and improve the new hire’s Day 1 experience.
- Organizations can achieve improved compliance posture by transitioning to alternative IGA solutions, with real-time SoD analysis, audit-ready dashboards, policy enforcement trails, and automated access certifications, which move them away from periodic audit to continuous compliance.
- Organizations can break down SAP Silos by moving to IGA tools offering cross-enterprise governance aligned features, ensuring the security policy enforcement and access provisioning across SAP and non-SAP applications simultaneously.
Final Considerations Before Making a Decision
The transition from SAP Identity Management is a strategic decision that will determine an organization’s security posture and operational efficiency for the next decade. They should weigh the final considerations below before finalizing IAM/IGA vendor selection.
Solution should align with long-term identity governance strategy.
Organizations should align the alternative solution with their long-term governance strategy; seeing that the tool can integrate with SAP is not enough. The solution should ensure it can support Zero Trust principles and a bundle of integrated identity services covering workforce, customers, partners, and machine identities across hybrid and cloud environments. Asking questions about emerging technologies like Decentralized Identity, AI-driven Threat Detection, and Verifiable Credentials, and whether R&D is in place to further incorporate them into solutions in the future.
Avoid a tool-only replacement mindset.
Organizations often make the mistake of treating migration as only existing SAP IDM processes being transferred to the new platform, not knowing that if existing processes are broken or data is not cleaned, the new system will break too, or only provide those inefficient processes carried over. The strategic goal should be to re-engineer processes, eliminate redundant workflows, or simplify workflows before transitioning to the new system, rather than wondering how we do that in the new tool or considering why we should do it the same way, aiming for simpler, standardized workflows.
Balance customization vs. standardization
Organizations should stick to out-of-the-box features as much as possible by adopting a clean core philosophy with balanced customization and standardization, rather than fully replicating existing customizations. For example, they should try to change the business process as much as possible rather than bringing heavy customization to a new tool, or adopt the 80/20 rule: 80% for standardization and 20% for the core, unavoidable business processes with customization.
Consider internal capability maturity.
Shifting from extensively customized on-premises processes to a cloud-native, configuration-driven solution requires a different skillset. The strategic goal should be to assess your existing teams to determine whether they have the capabilities needed; otherwise, extensive retraining or hiring new talent would affect the TCO, such as bringing in people familiar with platforms like Saviynt or SailPoint, or experts in REST/SCIM API integrations.
Start early due to multi-year timelines.
Recognizing that a typical enterprise IGA migration would take 18 to 36 months to complete, waiting for mainstream and extended maintenance deadlines will likely result in high implementation costs and a shortage of qualified partners. The strategic goal should be to start early with a phased approach, using a low-risk transition and a parallel run of both SAP IDM and the new solution, rather than rushing to migrate later, which could lead to audit failures and security gaps.
Conclusion
The upcoming SAP IDM sunset marks a strategic inflection point for organizations that rely heavily on SAP provisioning, governance, and lifecycle automation. Organizations are encouraged to rethink their identity and access management strategies, not just technical replacement, but as an opportunity for modernizing their identity security and governance aligned with broader business goals and the IAM landscape shift.
Alternative IAM/IGA solutions vary by architecture, cost, customization, and ecosystem alignment, with a diverse set of market leaders. Examples include the ecosystem-consolidation-driven Microsoft Entra ID and Pathlock Cloud, a leader in deep SAP-specific, compliance-oriented, and Application Access Governance capabilities.
As a full IAM migration is typically a multi-year project, early vendor evaluation ensures a competitive advantage and a smoother transition. Organizations that have started early assessments may have secured the best implementation partners and avoided high costs before deadlines. The right solution choice depends on the SAP footprint, including evaluating how much business relies on SAP, determining the enterprise architecture (whether it is cloud-first, on-prem, or hybrid), and assessing the level of SAP integration. Either they face intense regulatory requirements, e.g., GDPR or SOX, have internal qualified teams to manage complex systems, or need a standard SaaS solution with proper training and documentation. Organizations can replace SAP IDM with a solution that meets their current needs and supports future growth by carefully evaluating the above factors and following a structured migration roadmap.