This is the online edition of the ERP Market Insights Newsletter by David Vincent.
Agility is the name of the game in today’s ERP data security landscape. Being able to continuously monitor and detect anomalies and threats as they happen and quickly respond with an effective mitigation action is critical to maintaining a security posture. However, getting there is a challenge. One strategy that is helping organizations become more proactive is aligning to an adaptive security model.
What Is Adaptive Security?
Briefly, adaptive security is an approach to managing security that analyzes user behaviors against policy requirements to detect anomalies and threats before they happen. With an adaptive security model, an organization can continuously assess (monitor) key risk indicators and respond by automatically providing an adequate risk mitigation response that could be dialed up or down to fit the need.
The Challenges To Implementing Adaptive Security
The foundation of your adaptive security capability must be based on a security model capable of enabling an adaptive security response, which cannot be achieved with the static role-based access control (RBAC) security model.
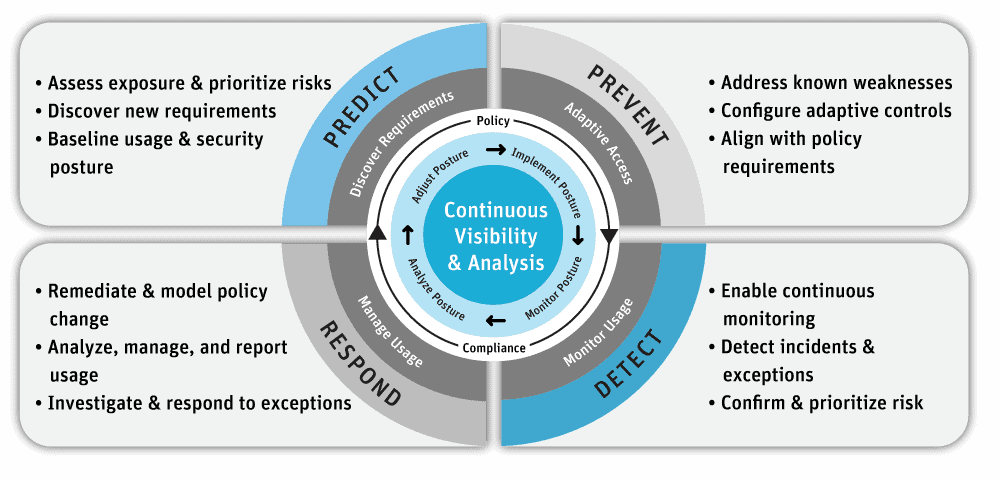
Gartner describes four control capabilities required to achieve an effective adaptive security architecture:
- Prediction
- Prevention
- Detection
- Response
Prevention and detection have been key pillars of a traditional approach to cybersecurity for many years. Still, Gartner mentions that many organizations’ current incident response mindset, which views security incidents as one-off events, must shift to a continuous response capability.
Organizations must assume they will be compromised. Continuous monitoring of the relevant key risk indicators is the only way to reliably detect and respond to anomalies and threats before it is too late.
Here’s the main problem: you cannot achieve an adaptive security model with the static role-based access control (RBAC) security model found in most ERP systems (i.e., SAP, PeopleSoft, Oracle EBS, etc.). Instead, context-aware security (also known as attribute-based access controls or ABAC) that uses situational information, such as identity, geolocation, time of day, or type of endpoint device, is required.
Gartner recommends transitioning from the static RBAC security model to an ABAC security model. The customer configures adaptive security using combinations of contextual attributes to enforce security, risk, and compliance policy requirements into each access, transaction, and data field level control, thus automating policy enforcement.
The Seven CARTA Imperatives For Achieving Adaptive Security Model
According to Gartner, supporting digital business transformation in an environment of advanced threats requires an innovative approach for all facets of security. Gartner calls this strategic approach “continuous adaptive risk and trust assessment,” or CARTA, which is focused on standardizing agile, enabling contextual awareness, and leveraging adaptive security technologies to enable organizations to strengthen security and leverage automation for continuous improvement.
Each CARTA imperative is Gartner’s recommended capability required of your ERP security, risk, and compliance solution to enable the security model.
1. Replace One-Time Security Gates with Context-Aware, Adaptive, and Programmable Security Platforms
Organizations need to replace the initial one-time, yes/no risk-based decision at the main gate to their systems (typically managed by a static authentication and authorization process) with a continuous, real-time, adaptive risk and trust analysis of user anomalies with context-aware information across the platform. There is a reason Gartner listed this as the first imperative. The foundation of your adaptive security capability must be based on a security model capable of enabling an adaptive security response. In other words, ABAC instead of RBAC.
2. Continuously Discover, Monitor, Assess, and Prioritize Risk — Proactively and Reactively
Risks events are fluid and require constant identification, analysis, prioritization, monitoring, and response after the initial login assessment. This should include a combination of proactive and reactive capabilities. For example, if a user attempts to download a large amount of sensitive data, you need the ability to detect and prevent this action if it’s considered inappropriate.
3. Perform Risk and Trust Assessments Early in Digital Business Initiatives
This imperative focuses on early risk assessment, meaning performing risk and trust assessments early in the process execution.
4. Instrument Infrastructure for Comprehensive, Full Stack Risk Visibility, Including Sensitive Data Handling
This is a continuous risk assessment recommendation across the full tech stack and data handling to enable adaptive security decisions.
5. Use Analytics, AI, Automation, and Orchestration to Speed the Time to Detect and Respond, and to Scale Limited Resources
This imperative recommends using artificial intelligence, machine learning, analytics, and automation to increase the efficiency and effectiveness of risk detection, analysis, and response capabilities.
6. Architect Security as an Integrated, Adaptive Programmable System, Not in Silos
Avoid silos! Organizations shouldn’t perform risk assessments in individual isolated silos. Instead, aggregate continuous risk assessments provide a more accurate view of the organizations’ risk exposure.
7. Put Continuous Data-Driven Risk Decision Making and Risk Ownership into Business Units and Product Owners
This imperative encourages better transparency and decision-making through better data-driven risk visibility to the business unit leaders for their own decision-making.
A couple of items worth mentioning that are not included in the seven imperatives (but I think are important):
Establish Effective Governance – The organization should establish a Tone at the Top with Board-level oversight to enable effective governance over the adaptive security program. ISO 38500 and ISO 27001’s clauses 5, 6, and 7 define leading practices for establishing an effective governance structure.
Continuous Improvement – The effectiveness of the CARTA Program should be evaluated semi-annually through self-assessments and independent assessments to identify opportunities to correct problems and make improvements. ISO 27001’s clause 10 defines requirements for continual improvement, and ISO 27001’s section 5.7 provides guidance on performance evaluation.
Conclusion
Adaptive security enabled by the ABAC security model supports the principles of Least Privilege, Defense in Depth, and Zero-Trust with preventative & detective controls at various levels: access, transaction, and data fields. Furthermore, adaptive security constantly monitors the key risk indicators in the form of policy requirements configured into the access controls and dynamically adapts to respond to threats with the appropriate mitigation action.
I hope this provides some clarity into the term Adaptive Security. The capabilities mentioned above exist within the Pathlock Platform, allowing security professionals to easily configure their system and data security with an adaptive security model.



