In the field of information technology security, it’s imperative to gain a thorough understanding of the Vulnerability Management Lifecycle (VML).
What is Vulnerability Management Lifecycle ?
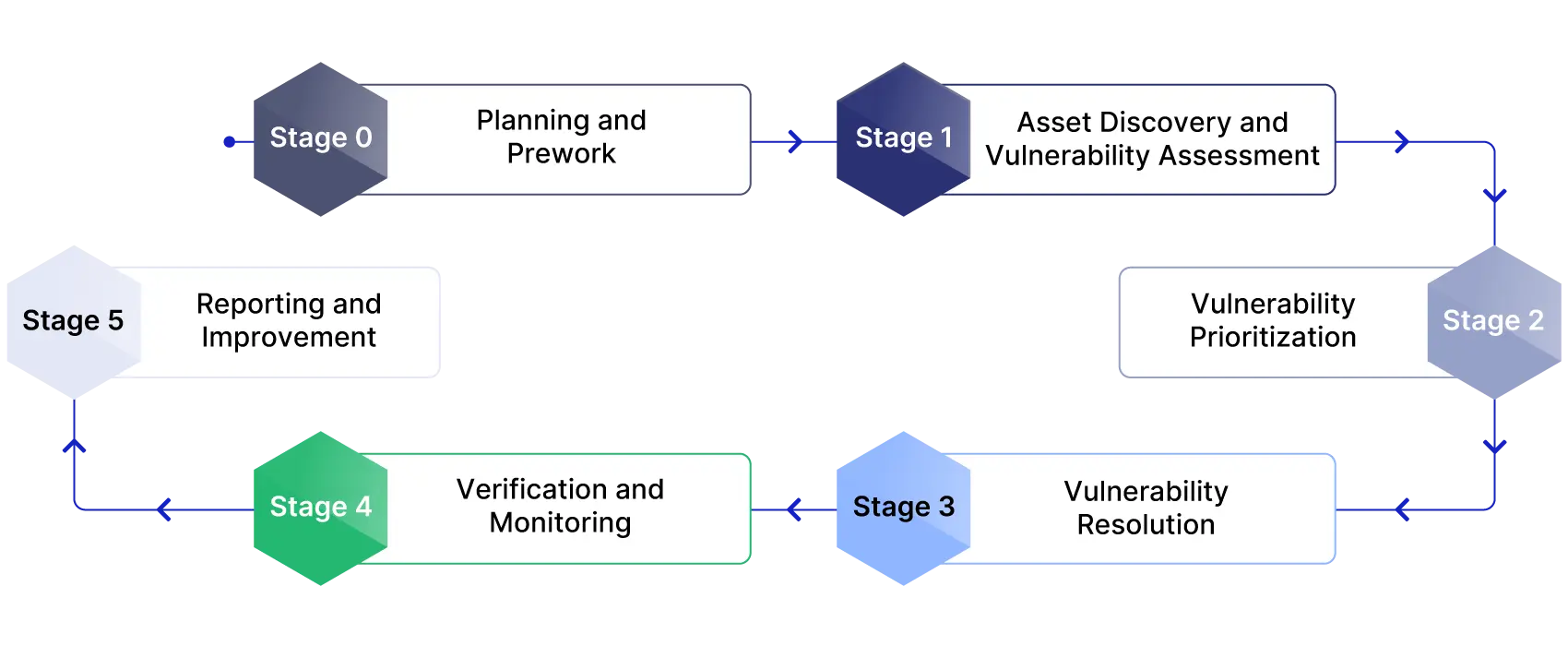
The Vulnerability Management Lifecycle is an ongoing method that identifies, assesses, classifies, and addresses flaws within a company’s IT infrastructure. This recurring, circular procedure substantially improves the safety of corporate data and devices.
The frequency of cyberattacks is on the rise. These attacks are also becoming increasingly complex. By embracing a methodical strategy such as the VML, IT teams can minimize potential hazards and protect their networks and their valuable data.
Six Stages of Vulnerability Management Lifecycle
The Vulnerability management lifecycle process is an ongoing cycle created to proactively improve measures for cybersecurity. There are multiple phases in the process, each playing a critical role in enhancing the efficiency of managing vulnerabilities.
Stage 1: Planning and Pre-work
Stage 0, Planning and Pre-work, lays the foundational framework for the Vulnerability Management Lifecycle (VML). This stage ensures that organizations establish a structured approach and allocate the necessary resources to manage vulnerabilities effectively. By defining roles, setting benchmarks, and outlining criteria for handling vulnerabilities, this stage sets the tone for a successful VML implementation.
Establish Stakeholders and Roles
The first step in this stage involves identifying and establishing key stakeholders along with their associated roles. These individuals, typically drawn from IT, security, and leadership teams, are responsible for driving the Vulnerability Management Lifecycle process and ensuring alignment with organizational goals.
Allocate Resources
Additionally, this stage involves distributing the necessary resources for VML, including personnel, tools, and funding, to support ongoing operations and decision-making.
Success Metrics
Benchmarks for success are developed to measure the effectiveness of the VML process. These benchmarks include:
- Average Time to Action: The average time taken to respond to identified vulnerabilities.
- Mean Time to Remediation: The average time required to resolve vulnerabilities.
- Risk Score: A measure of the overall risk associated with identified vulnerabilities.
- Acceptance Risk Score: The level of risk deemed acceptable by the organization.
- Average Vulnerability Age: The average time vulnerabilities remain unresolved.
Guidelines for Handling and Ranking Vulnerabilities
Another critical aspect of this stage is developing clear criteria for handling and ranking vulnerabilities. Organizations evaluate potential weaknesses based on factors such as:
- Severity of the vulnerability
- Asset criticality and business impact
- Threat intelligence and likelihood of exploitation
- Exposure level within the IT environment
- Compliance and legal requirements
- Remediation effort required to address the issue
- Historical context, including past incidents and trends
- Cost-benefit analysis of remediation efforts
- Dependencies and chain vulnerabilities
- Organizational risk appetite
By establishing a robust foundation in Stage 0, organizations ensure a consistent and strategic approach to vulnerability management. This planning phase is essential for streamlining subsequent stages and enabling a proactive response to emerging threats.
Stage 2: Asset Discovery and Vulnerability Assessment
In Stage 1, Asset Discovery and Vulnerability Assessment, organizations focus on identifying and evaluating their IT environment to gain comprehensive visibility into all assets and uncover potential weaknesses. Building on the foundational work in Stage 0, this stage ensures a clear understanding of what needs protection and lays the groundwork for effective vulnerability management.
Stage 1 essentially involves following two steps:
- Create and maintain a dynamic inventory of Assets
- Classify assets based on their role in business
Let’s look at each of these two steps:
Create and Main Dynamic Inventory
The process begins with creating and maintaining a dynamic inventory of all IT assets, including hardware, software, network devices, cloud resources, and IoT devices. Shadow IT—unauthorized or unknown assets—must also be identified to eliminate blind spots.
Classify Assets
Each asset is then categorized and classified based on its role in business operations, data sensitivity, and potential impact. Frameworks like the Center for Internet Security (CIS) or custom criteria can guide this classification process.
Perform Vulnerability Scans
Organizations perform vulnerability scans across the asset inventory to detect known vulnerabilities. These scans should encompass on-premises, cloud, and hybrid environments to ensure complete coverage.
Conduct Penetration Testing
In addition to automated scans, periodic penetration testing simulates real-world attacks to identify exploitable vulnerabilities that automated tools may miss. Further assessments include reviewing system configurations against security baselines and identifying outdated patches that could expose systems to risk.
Success Metrics
Success Metrics for Stage 1 of Vulnerability Management Lifecycle include following:
- Asset Discovery Completeness: The percentage of total assets identified and inventoried.
- Vulnerability Coverage: The proportion of assets scanned for vulnerabilities.
- Detection Accuracy: The number of vulnerabilities accurately identified versus false positives.
- Time to Discovery: The average time taken to identify and log new or shadow assets.
Organizations face challenges such as dynamic environments, incomplete data due to poor integration between tools, and limited resources for conducting and analyzing scans. By addressing these obstacles, a thorough and well-executed asset discovery and vulnerability assessment process ensures organizations understand their critical assets and greatest risks, setting the stage for effective prioritization and resolution.
Stage 3: Vulnerability Prioritization
Stage 2, Vulnerability Prioritization, focuses on analyzing and ranking identified vulnerabilities to address the most critical risks first. This stage ensures that vulnerability remediation efforts align with business priorities and security needs, optimizing resource allocation for maximum impact. Following are four steps involved in vulnerability prioritization:
- Conduct a risk assessment to evaluate vulnerabilities
- Quantify the security of vulnerabilities by CVSS framework
- Conduct vulnerability contextual analysis to determine system dependencies and recent threat activity
- Categorize vulnerabilities by the complexity of remediation efforts
Let’s look at each of the following.
Conduct a Risk Assessment
Organizations begin by conducting a risk assessment to evaluate vulnerabilities based on following factors:
- Severity
- Exploitability
- Potential impact
- Likelihood of occurrence
Quantify Severity of Vulnerabilities
Established frameworks like the Common Vulnerability Scoring System (CVSS) help quantify the severity of vulnerabilities. Next, vulnerabilities are assigned criticality ratings that incorporate factors such as:
- Asset value
- Threat intelligence
- Exposure level.
This step ensures that the risks to the most important assets are prioritized effectively.
Conduct Vulnerability Contextual Analysis
Contextual analysis is another vital step, incorporating information such as system dependencies, recent threat activity, and organizational risk appetite. Organizations also evaluate chain vulnerabilities, which may escalate risk when combined with others. Real-time threat intelligence is integrated to adjust priorities dynamically, focusing on vulnerabilities actively exploited in the wild.
Categorize Vulnerabilities
Finally, vulnerabilities are categorized by the complexity of remediation efforts, with priority given to high-impact, low-effort issues.
Success Metrics
Success metrics for completion of Stage 2 include the following:
- Prioritization Accuracy: The percentage of high-severity vulnerabilities effectively ranked and addressed.
- Risk-Weighted Scoring: The use of weighted formulas incorporating CVSS, business impact, and threat intelligence.
- Time to Prioritize: The average time taken to categorize and rank vulnerabilities after discovery.
- Remediation Feasibility: The proportion of prioritized vulnerabilities addressed within available resources.
Challenges in this stage include managing the volume of detected vulnerabilities, adjusting to a dynamic threat landscape, and balancing technical severity with real-world impact. By addressing these challenges, organizations can strategically minimize the likelihood of exploitation, optimize their response capabilities, and enhance their overall cybersecurity resilience.
Stage 4: Vulnerability Resolution
Stage 3, Vulnerability Resolution, focuses on taking decisive action to address prioritized vulnerabilities. The objective is to reduce or eliminate risks effectively, strengthening the organization’s security posture while minimizing disruptions to operations. This stage involves selecting the most appropriate resolution strategies, coordinating efforts across teams, and leveraging tools to enhance the efficiency of the process.
The first step in this stage is determining the optimal approach for each vulnerability. Organizations can choose among three main strategies:
- Remediation: Fully resolving the issue by applying patches or updates to eliminate the vulnerability.
- Mitigation: Reducing the risk by implementing compensating controls, such as firewalls or access restrictions.
- Risk Acceptance: Acknowledging and accepting low-impact vulnerabilities when remediation is impractical or unnecessary.
These decisions should be guided by business priorities, compliance requirements, and the organization’s overall risk tolerance. Once the resolution strategy is defined, organizations execute actions such as patch management, configuration adjustments or compensating controls. Let’s have a look at each of execution based on resolutions strategies in the following table:
Collaboration and communication play a pivotal role in successful vulnerability resolution. IT, security, and business teams must coordinate their efforts to plan and execute remediation actions effectively. Clear communication regarding timelines, potential impacts, and contingency plans ensures that operations are not disrupted. Automated tools further enhance the process by accelerating tasks like patch deployment and configuration updates, improving both speed and accuracy.
| Resolutions Strategy | Action to Execute |
|---|---|
| Remediation | Patch Management: Patching involves deploying updates to software, operating systems, and hardware to address known vulnerabilities. |
| Mitigation | Configuration Adjustments: Configuration changes focus on rectifying insecure system settings or permissions to enhance security. To avoid introducing new issues, patches should be tested in staging environments before being rolled out to production systems. |
| Risk Acceptance | Compensation Controls: For vulnerabilities that cannot be patched, compensating controls provide alternative risk reduction measures. |
Success Benchmarks for Stage 3 of VLM
Metrics such as Mean Time to Remediate (MTTR), resolution effectiveness, and minimal operational disruptions measure success in this stage. However, challenges like complex environments, resource limitations, and legacy systems can complicate the process. By addressing these vulnerabilities efficiently and collaboratively, organizations can promptly mitigate risks and reinforce their overall cybersecurity defenses.
Stage 5: Verification and Monitoring
Stage 4, Verification and Monitoring, ensures that the actions taken to address vulnerabilities are effective and sustainable. This stage focuses on validating corrective measures, identifying any remaining risks, and maintaining continuous surveillance to address emerging threats. It reinforces the cyclical nature of the Vulnerability Management Lifecycle (VML) by using insights gathered to improve future iterations.
Verify Effectiveness of Remediation or Mitigation
The first step in this stage is verification, which involves testing and validating the effectiveness of implemented remediation or mitigation strategies. Organizations assess whether vulnerabilities have been fully resolved or whether additional actions are needed. This step may include re-scanning systems, conducting penetration tests, or reviewing updated configurations to ensure that no gaps remain.
Continue Monitoring for New Vulnerabilities
Monitoring is the ongoing process of tracking the security environment for new or recurring vulnerabilities. Automated tools and real-time alerts play a key role in maintaining vigilance, enabling organizations to detect emerging risks promptly. Regular vulnerability assessments and system health checks help ensure that newly identified threats are addressed before they can cause harm.
Incorporate Feedback into the Next Lifecycle
This stage also emphasizes the importance of documentation and reporting. Organizations should record the outcomes of remediation efforts, the effectiveness of actions taken, and any lessons learned. These insights are critical for refining future cycles of the VML, enabling more efficient and proactive approaches to vulnerability management over time.
Success Metrics
Success in Stage 4 is measured by metrics including:
- Remediation Validation Rate (the percentage of resolved vulnerabilities successfully verified as closed)
- Monitoring Coverage (the extent to which systems are continuously tracked for new risks)
- Incident Detection Time (the speed at which new vulnerabilities or threats are identified)
- Feedback Utilization (the incorporation of lessons learned into future VML cycles).
By thoroughly verifying remediation efforts and maintaining vigilant monitoring, organizations ensure that their security posture remains strong and adaptive. Stage 4 not only confirms the effectiveness of current efforts but also lays the groundwork for continuous improvement, reinforcing resilience against evolving cybersecurity threats.
Stage 6: Reporting and Improvement
Stage 5 (Reporting and Improvement) is the final phase of the Vulnerability Management Lifecycle (VML). It emphasizes on the importance of documentation, communication, and continuous process enhancement. This stage consolidates the outcomes of previous efforts and provides insights to refine future VML cycles, ensuring that vulnerability management evolves alongside the threat landscape.
Comprehensive Reporting
The first step in this stage is comprehensive reporting, which involves documenting the outcomes of remediation efforts, validation processes, and monitoring activities. Reports should include details such as resolved vulnerabilities, outstanding issues, and metrics like Mean Time to Remediate (MTTR) or Remediation Validation Rate. These reports not only provide a clear picture of the organization’s security posture but also serve as a record for compliance audits and stakeholder transparency.
Communication
Communication is another critical component of this phase. The findings and results from the VML should be shared with relevant stakeholders, including IT teams, security personnel, and executive leadership. Tailored reporting ensures that each group receives actionable insights appropriate to their role, helping them make informed decisions. For example, technical teams might receive in-depth vulnerability data, while executives might focus on high-level trends and strategic recommendations.
Process Improvement
Finally, process improvement is key to strengthening the VML over time. Organizations should evaluate the performance of each stage, identifying bottlenecks, inefficiencies, or areas for enhancement. Lessons learned from previous cycles—such as the effectiveness of remediation strategies or the speed of vulnerability detection—can inform adjustments to tools, workflows, and resource allocation. This feedback loop ensures the VML becomes more efficient and effective with each iteration.
Frameworks and Standards for Vulnerability Management
Following are some the vulnerability management frameworks and standards:
NIST SP 800-40
Creating a sturdy Lifecycle for Vulnerability Management can be done through pre-existing structures and professional norms. An example of this is the Special Publication 800-40 from the National Institute of Standards and Technology, commonly known as NIST SP. This model provides a detailed pathway for all-encompassing patch management, with an emphasis on locating assets, evaluating potential risks, and documenting the results.
Industry-Specific Standards
More specific guidelines can be provided through standards such as ISO 27001 from the International Organization for Standardization, or the Payment Card Industry Data Security Standard (PCI DSS). Such standards offer specialized guidance, aiding companies in establishing effective procedures for managing vulnerabilities, thereby improving their security.
Pros of Vulnerability Management Lifecycle
Proactive Defense Mechanism
The life cycle of Vulnerability Management serves as a pre-emptive safeguarding strategy for an entire corporation. Rather than simply responding to dangers, it enables IT teams to foresee and deal with them.
The core of the VML is persistent surveillance and immediately addressing identified weaknesses. By assessing an IT network, VML offers up-to-date data to address potential shortcomings, thus reducing the likelihood of cyber threats succeeding.
Strategic Resource Allocation
Strategic resource distribution is yet another benefit provided by the VML. This allows for the effective ranking of potential risks based on their degree of threat. Consider it similar to a hospital’s prioritizing system, where critical patients get immediate attention. Likewise, serious security issues are addressed with the greatest sense of urgency. This guarantees efficient use of resources, focusing on the dangers that present the most significant risk to a network and corporate data.
Regulatory Compliance
The VML does more than just to protect the network and IT resources. Adhering to the VML paves the way for a business to be in sync with benchmarks and frameworks such as:
- NIST SP 800-40
- ISO 27001
- PCI DSS.
Meeting regulatory obligations and demonstrating a strong commitment to cybersecurity and to stakeholders is critical in today’s business environment.
Enhanced Incident Response
Additionally, the incident response efforts of an organization can be enhanced by the VML. Knowing weak points in case of a cyberattack enables a quicker, more efficient reaction. A developed VML can offer crucial understanding that assists in designing a robust incident response strategy.
Security Awareness Culture
Promoting a sense of security awareness within corporations is also a fundamental task of the VML. Regular evaluations and ongoing scrutiny of potential risks guarantees that maintaining safety is a top concern for all involved.
By adopting this method, a “security awareness culture” is instilled, improving the total security posture of the entire company.
Cons of Vulnerability Management
Resource Constraints
Even though it is critical to IT security, the execution of the Vulnerability Lifecycle Management program typically faces numerous obstacles. The scarcity of both human and financial resources poses a major challenge. That’s why a balance of automation, tools, and systems combined with manual labor is the best path forward.
Inefficiencies
Effective management of vulnerabilities can also be compromised if there is a lack of alignment between IT and security teams. The organization’s security posture could be at risk of compromise if potential critical vulnerabilities are missed due to poor cooperation among these teams.
Time Consumption
Managing vulnerabilities might be quite time-intensive, particularly in relation to patching and handling manual procedures. Delaying the patching process might prolong fixing identified weaknesses, paving the way for additional, larger cyber risks.
Best Practices for Vulnerability Management
Maintain an Updated Asset Inventory
Effective vulnerability management primarily depends on the maintenance of a current asset inventory. This requires the regular and timely upgrading of both hardware and software infrastructure owned or used by a company, enabling the rapid detection and handling of potential threats.
Regular Vulnerability Scans
Another recommended procedure is to routinely perform vulnerability scans. Routine examination of IT infrastructures can enable prompt identification of weak points and risks, thereby preventing possible security intrusions and loss of information.
Streamlined Patch Management Processes
Improving the efficiency of patch management procedures plays a huge role in managing vulnerabilities. Prompt patching can shrink the time gap from the moment a vulnerability is found to its fix, reducing the likelihood of cyber attackers and hackers taking advantage of these known frailties.
Frequent Security Training for Employees
Negligent or angry employees are perhaps the greatest threat to a business’s IT infrastructure. As a result, it is crucial to offer consistent safety instruction to employees and staff. By sharing knowledge about current cyber threats and their countermeasures, this training cultivates a culture of security in an organization.
Use Automated Tools for Efficiency
The use of automated instruments greatly improves precision and effectiveness in handling security risks. Compared to manual techniques, these instruments identify security risks with increased speed and accuracy.
Incorporate Vendor and Third-party Assessments
By incorporating evaluations of vendors and third parties into a security vulnerability plan, businesses can recognize risks from outside sources. Making sure these groups adhere to safety guidelines lowers the chance of system weakness being introduced.
Tools for Vulnerability Management Lifecycle
Integration of Advanced Tools
The Vulnerability Management Lifecycle is being advanced through the use of contemporary tools with Pathlock Cloud. With easy-to-use interfaces, these tools (and others like them) provide a comprehensive solution for managing vulnerabilities. They monitor systems and detect emerging weaknesses, from identifying assets to assessing vulnerabilities and ranking threats.
Benefits of Automated Solutions
The significance of automation in the field of vulnerability management cannot be understated, as it considerably enhances precision and productivity. Automation speeds up the detection and remediation processes, greatly narrowing the window in which a vulnerability can be exploited by bad actors.
Leveraging AI and ML for Enhanced Threat Detection
The domain of vulnerability management is undergoing a transformation due to advancements in Artificial Intelligence (AI) and Machine Learning (ML). They have the capability to rapidly scrutinize vast amounts of data, recognize trends, and forecast potential dangers. The ability to quickly process data leads to more precise forecasts of threats, boosting the overall performance of the VML.
Continuous Improvement in Vulnerability Management
Feedback Loops to Refine Processes
Ongoing improvement is important for managing vulnerabilities effectively. Setting up feedback systems can offer a better understanding of how successful the reduction tactics are and the level of security within a business.
Use of Lessons Learned for Future Lifecycle Iterations
Improvements in the future can be informed by understanding obtained from past lifecycle stages. This essential data aids in enhancing the procedures of identification, ranking, and solving.
Monitoring Emerging Trends in Cybersecurity Threats
Staying up to date with the latest trends in cybersecurity is every bit as important as anything else. In response to the rapid evolution of online security threats, it is key to appropriately adjust and modernize approaches to managing vulnerabilities. Taking a forward-thinking strategy guarantees strong and efficient protection against new and evolving risks.
Real World Applications of VML
Health Care Industry
Healthcare providers leverage VML to secure electronic health record (EHR) systems and protect patient data under regulations like HIPAA. By prioritizing vulnerabilities in medical devices and IT infrastructure, these organizations mitigate risks such as ransomware attacks and ensure uninterrupted patient care.
Manufacturing Industry
Similarly, manufacturing industries use VML to secure their operational technology (OT) systems and IoT devices, which are critical to production processes. Identifying and addressing high-risk vulnerabilities in these systems prevents costly disruptions and cyber sabotage, strengthening the resilience of their operations.
Retail Industry
In retail, VML safeguards customer data by securing payment platforms (including those on websites or apps) and point-of-sale systems. This reduces the risk of data breaches and improves customer trust, all while ensuring compliance with regulations like GDPR.
Public Sector
For government agencies, VML is a cornerstone for protecting critical infrastructure and sensitive national data. By addressing vulnerabilities in legacy systems and implementing continuous monitoring, agencies strengthen their defense against large-scale cyberattacks, ensuring the safety of essential services and public trust. These examples highlight the necessity of VML in adapting to the unique cybersecurity challenges of different sectors.
Conclusion
The Lifecycle of Vulnerability Management acts as a sturdy protective measure against the increasing surge of cyber threats. VML combines regular surveillance, efficient utilization of resources, compliance with regulations, and a better approach to incident response into a single integrated entity. Additionally, it fosters a focus on security within a company, strengthening its ability to withstand cyberattacks.
Utilize VML to sustain alertness, encourage development, and progress towards a technologically advanced environment that not only defends against potential dangers but also smartly maneuvers to defeat them.
Pathlock offers industry-leading solutions to automate and streamline the Vulnerability Management Lifecycle, helping protect critical business applications and sensitive data.
Take the next step in securing your organization—book a demo with Pathlock today. Let us show you how Pathlock can help you safeguard your business against ever-evolving cyber threats.
Definition of Key Terms
Vulnerability Management Lifecycle (VML):
A recurring process designed to identify, assess, classify, and resolve security vulnerabilities in IT systems to enhance cybersecurity.
Criticality Ratings (CVSS, MITRE CVE):
Standardized metrics to measure the severity of vulnerabilities, such as the Common Vulnerability Scoring System (CVSS) or the MITRE Common Vulnerabilities and Exposures (CVE).
Mean Time to Detect (MTTD):
The average time taken to identify a security vulnerability or threat.
Mean Time to Remediate (MTTR):
The average time taken to resolve a security vulnerability after detection.
NIST SP 800-40:
A framework developed by the National Institute of Standards and Technology for enterprise patch management and vulnerability assessment.
ISO 27001:
An international standard for information security management systems, providing guidelines to secure IT environments.
PCI DSS:
The Payment Card Industry Data Security Standard, a set of security standards to protect cardholder data and ensure secure payment systems.
FAQ: Vulnerability Management
1. What is vulnerability management?
It’s the process of identifying, evaluating, and remediating areas of vulnerability or weakness in IT systems to prevent cyberattacks.
2. What is the Vulnerability Management Lifecycle (VML)?
The vulnerability management lifecycle (VML) is a continuous process to plan, find vulnerabilities, prioritize fixes, resolve issues, and monitor for new threats.




