
As cyberattacks across the world increase in frequency and sophistication, companies are constantly working to improve detection capabilities, discover hidden vulnerabilities, and implement security strategies to counter modern attacks. In an effort to help government departments and private organizations improve their cybersecurity measures, the National Institute of Standards and Technology (NIST) published a set of rules, guidelines, and standards known as the NIST Cybersecurity Framework. Originally intended as just guidelines, the framework has become the gold standard for building a cybersecurity program across industries.
What Is The NIST Cybersecurity Framework (CSF)
NIST Cybersecurity Framework is a leading practice guidance on how both internal and external stakeholders of organizations can manage and reduce cybersecurity risks. It lists organization-specific and customizable activities associated with managing cybersecurity risk and it is based on existing standards, guidelines, and practices. According to Gartner, as of 2015, 30% of U.S. organizations use the NIST Cybersecurity Framework, and this is expected to rise to 50% by 2020.
Cybersecurity Framework History
- February 2013 – Executive Order 13636: Improving Critical Infrastructure Cybersecurity
- December 2014 – Cybersecurity Enhancement Act of 2014 (P.L. 113-274)
- May 2017 – Executive Order 13800: Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure
The Three Primary Components Of The NIST CSF
The Cybersecurity Framework consists of three main components:
- Core – Desired cybersecurity outcomes are organized in a hierarchy and aligned to more detailed guidance and controls.
- Profiles – Alignment of an organization’s requirements and objectives, risk appetite, and resources using the desired outcomes of the Framework Core.
- Implementation Tiers – A qualitative measure of organizational cybersecurity risk management maturity level.
The NIST CSF Framework Explained
The NIST CSF is composed of 5 functions, 23 categories, and 108 subcategories. The subcategories represent the desired outcomes and are the baseline for the NIST CSF assessment to evaluate the organization’s achievement of the desired outcomes. Each subcategory statement is based on leading practices from informative references like COBIT 5, ISO 27001:2031, NIST 800-53 Rev 4, ISA, CIS CSC, ISA 62443-2-1:2009, and ISA 62443-3-3:2013. They are meant to provide organizations with a starting point for implementing practices to achieve the Framework’s desired outcomes.
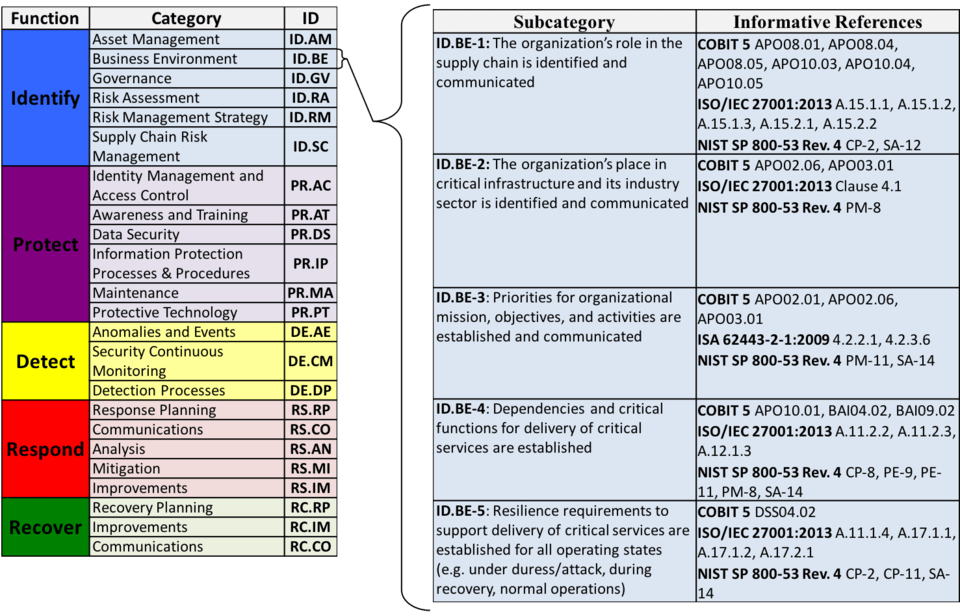
The NIST CSF Five Functions Explained
These 5 functions are not only applicable to cybersecurity risk management, but also to risk management at large.
1. Identify – Organizations must first fully understand their current environment to ensure they can successfully manage arising cybersecurity threats at various levels, including data, systems, and assets. Conducting a NIST Cybersecurity Framework assessment will help identify your risks within your industry or business context.
2. Protect – Once organizations have a better understanding of their cybersecurity risks, they can evaluate whether their cybersecurity safeguards offer sufficient protection, or if changes or additional controls are appropriate to ensure delivery of services.
3. Detect – Timely detection is crucial as it allows the proper threat mitigation response to be initiated quickly. The detection part of the NIST Cybersecurity Framework defines the essential processes necessary to identify cybersecurity events.
4. Respond – The NIST Cybersecurity Framework also includes the response domain that involves boosting the capacity of containing the adverse effects of cybersecurity events. It consists of all activities used by an organization once cybersecurity threats or incidents are detected.
5. Recover – This function allows you to highlight the best processes to achieve business resilience. It seeks to quickly restore impaired services, capabilities, and capacities to ensure everything is working as intended.
Framework Implementation Tiers
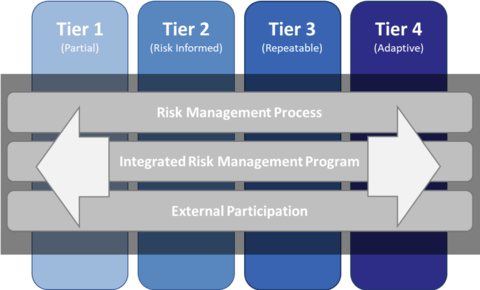
The four tiers illustrated below are used to represent the degree to which an organization’s cybersecurity risk management practices exhibit the desired outcome described in the 108-subcategory statement. The Tiers range from Partial achieved (Tier 1) to Adaptive (Tier 4).
Framework Profiles
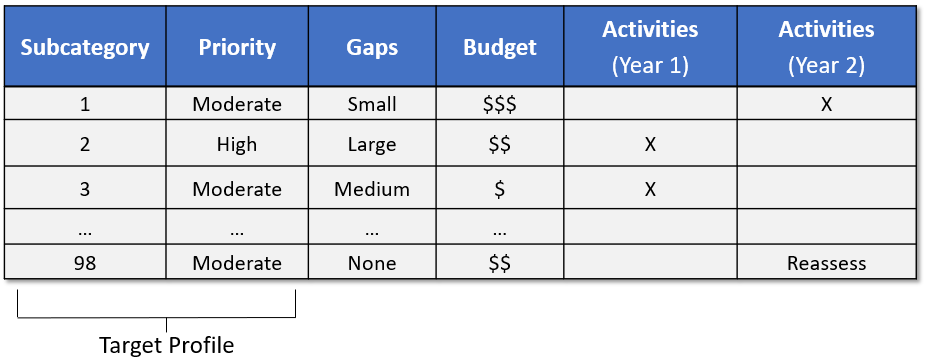
Profiles are an organization’s unique alignment of its organizational requirements and objectives, risk appetite, and resources against the desired outcomes of the Framework Core. Profiles can be used to identify opportunities for improving the organization’s current cybersecurity maturity levels by comparing a “Current” Profile with a “Target” Profile.
How Pathlock Solutions Align To The NIST Cybersecurity Framework For Managing Your ERP Landscape
| NIST CSF Functions | Pathlock Solution Capabilities |
| Identify | AI & ML Empowered Continuous Risk Analysis and Recommendations Engine Risk-Prioritized Exposure Reporting Individual User Behavior Usage & Access Profiling |
| Protect | Currently offering over 50 Configurable Settings via the Attribute-Based Access Controls (ABAC) Security Model ABAC Enabled Automated Policy Enforcement at the Business Process, Transaction, and Master Data Levels ABAC Enabled Preventative Control Capabilities at the Business Process, Transaction, and Master Data Levels – Enables business rule enforcement for Process Controls (rate-limiting, discounts, changes, total dollar amount, requirement of secondary review/approval, etc.) ABAC Enabled Risk-Adaptive Dynamic Security Responds to Anomalies and Incidents Data Loss Prevention – Apply dynamic data masking at the UI-level with a single rule, masks data in fields/tables/queries, and ensures users can only export data in secure environments Single Sign-On and Multi-Facture Authentication Integration |
| Detect | ABAC Enables Detailed User Behavior Analytic for Immediate Detections of Treats and User Anomalies Continuous Control Monitoring at the SOD (CCM-SOD), business transaction (CCM-T), and master data levels (CCM-MD) AI & ML Empowered Anomaly Detection & Reporting Automated Security Event Workflows |
| Respond | ABAC Enables Immediate Response to Detected Treats and User Anomalies Real-time Reporting Integrated with the CCM-SOD, CCM-T, and CCM-MD. Authorizations Impact Simulator – Models risk impact of authorization change request to roles and individual users, recommends best-fit alternatives and shows optional mitigations actions. Conflict Resolution Recommendations Engine – Automatically recommends the best-fit role when authorizations need to be removed from a user and solves SoD violations with recommendations that fix conflicts without losing necessary access. Audit Trail Forensics Reports – Captures a detailed audit trail with user usage and access context, and automatically delivered to the security manager upon a triggering event. |
| Recovery | Risk-Prioritized Exposure Reporting, Detailed User Behavior Analytic of Incidents and Anomalies, and AI & ML Empowered Recommendation Engine Enabling Effective Remediation Planning |



