Compliance-Centric
Identity Governance
When traditional IGA isn't enough, companies turn to
Pathlock for compliant provisioning, fine-grained SoD
analysis, user access reviews, privileged access, and
continuous controls monitoring.
Stories from Customers Around the Globe
Discover Pathlock Identity Security Platform
- Cross-app capabilities with 100+ connectors
- Out-of-the-box ruleset content
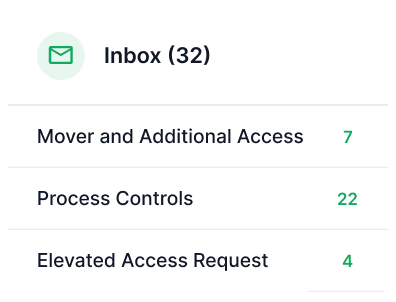
- Intuitive UI for reviewing and managing reported risks
- Flexible workflows
- Configurable individual portals (employee, third-party, etc.)
- Out-of-the-box workflows for common scenarios
- Inclusion of contextual HR, risk and usage data for better campaign results (20-30% revocation rates vs. 2-3%)
- Distributed administration of Certs (i.e. Third Party)
- Out-of-the-box workflows for common certifications
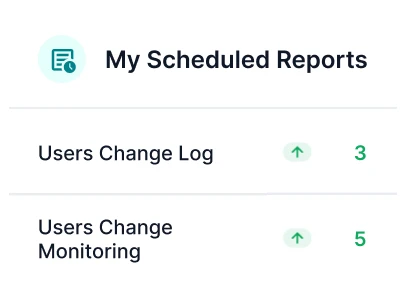
- Multi-app change log support
- Clear who changed what with “before” and “after” values
- Out-of-the-box content
- Dynamic role management with cross-application capabilities
- Streamlined role creation and optimization with automated suggestions
- Advanced analytics for role impact and compliance monitoring
Fine-Grained Governance for More Than 100 ERPs and Apps
Deployed in Partnership with the World’s Top Systems Integrators
“At KPMG, we are committed to innovation and collaboration, which is why we chose to collaborate with Pathlock — a leader redefining identity security…”

Go Beyond Traditional Identity Governance
Continuous Controls Monitoring
Automate financial and IT application controls testing. Be alerted on suspicious transactions and critical configuration changes.
-
Analyze SoD conflicts against real-time financial data
تعرّف على المزيد -
Detailed information on changes to master application data
تعرّف على المزيد -
Integrate and streamline control mechanisms from various frameworks into a centralized, automated system
تعرّف على المزيد
Analyze SoD conflicts against real-time financial data
تعرّف على المزيدDetailed information on changes to master application data
تعرّف على المزيدIntegrate and streamline control mechanisms from various frameworks into a centralized, automated system
تعرّف على المزيدCybersecurity Application Controls
Enforce data security controls and stop cybersecurity threats on your critical systems
-
Dynamically mask and anonymize data at the field level and at the point of access
تعرّف على المزيد -
Identify unaddressed risk in your SAP systems
تعرّف على المزيد -
Continuous monitoring for a wide range of internal and external threats
تعرّف على المزيد -
Continuously monitor the export and import of SAP transports
تعرّف على المزيد -
Protect sensitive information from unauthorized exposure
تعرّف على المزيد
Dynamically mask and anonymize data at the field level and at the point of access
تعرّف على المزيدIdentify unaddressed risk in your SAP systems
تعرّف على المزيدContinuous monitoring for a wide range of internal and external threats
تعرّف على المزيدContinuously monitor the export and import of SAP transports
تعرّف على المزيدProtect sensitive information from unauthorized exposure
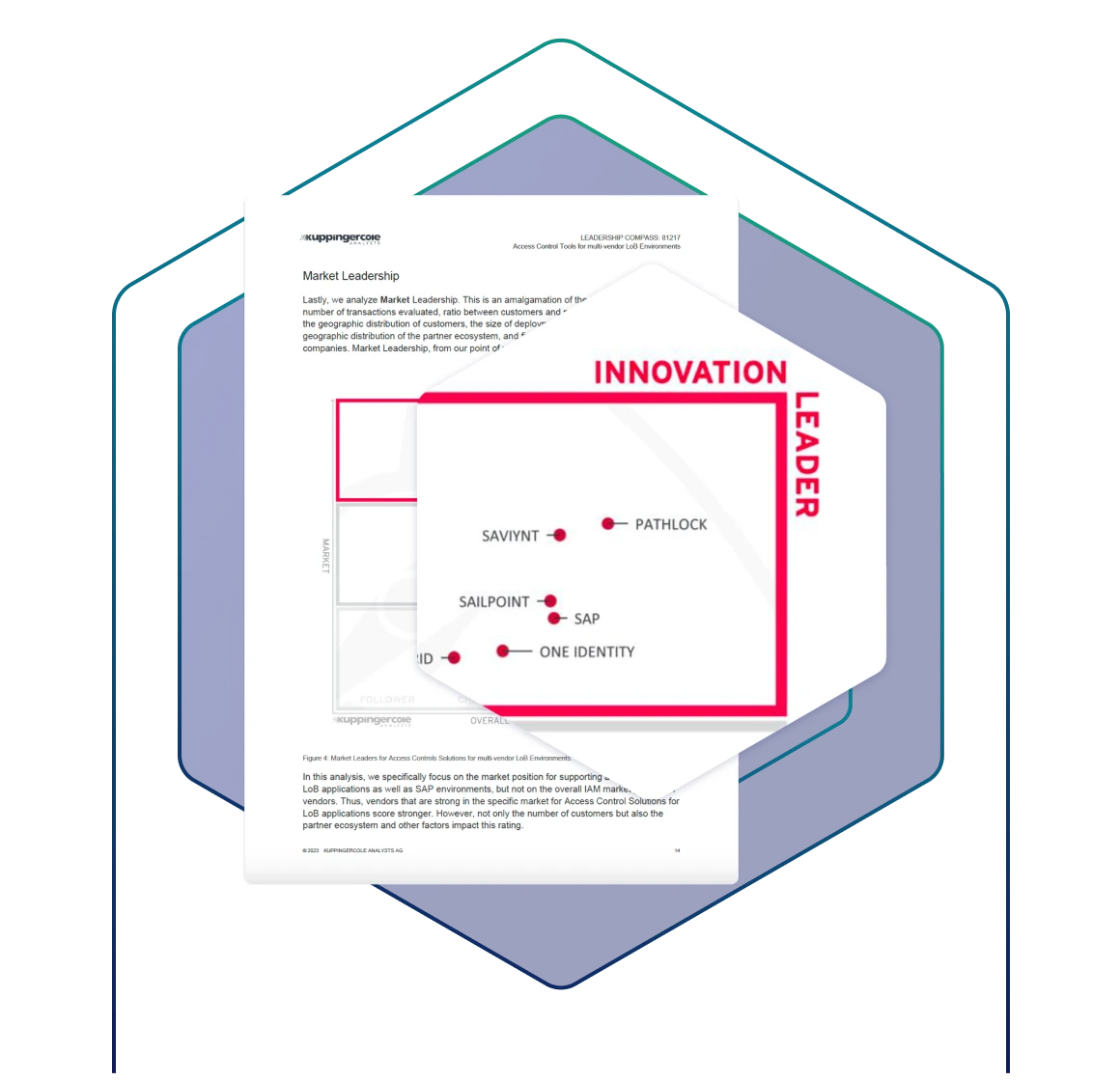
تعرّف على المزيدPathlock Recognized as a Leader in Access Control for Multi-App Environments
Get Expert Guidance on SAP Access Governance